
HTTP/2 Bomb DoS Hits Every Major Web Server Stack
HTTP/2 Bomb DoS exploits default configs on NGINX, Apache, IIS, and Envoy. Plus Acer Wave 7 CVSS 10.0 zero-days and a VS Code GitHub token stealer.
IT, Networking & Security — tutorials, guides, and insights.
Latest Posts

HTTP/2 Bomb DoS exploits default configs on NGINX, Apache, IIS, and Envoy. Plus Acer Wave 7 CVSS 10.0 zero-days and a VS Code GitHub token stealer.
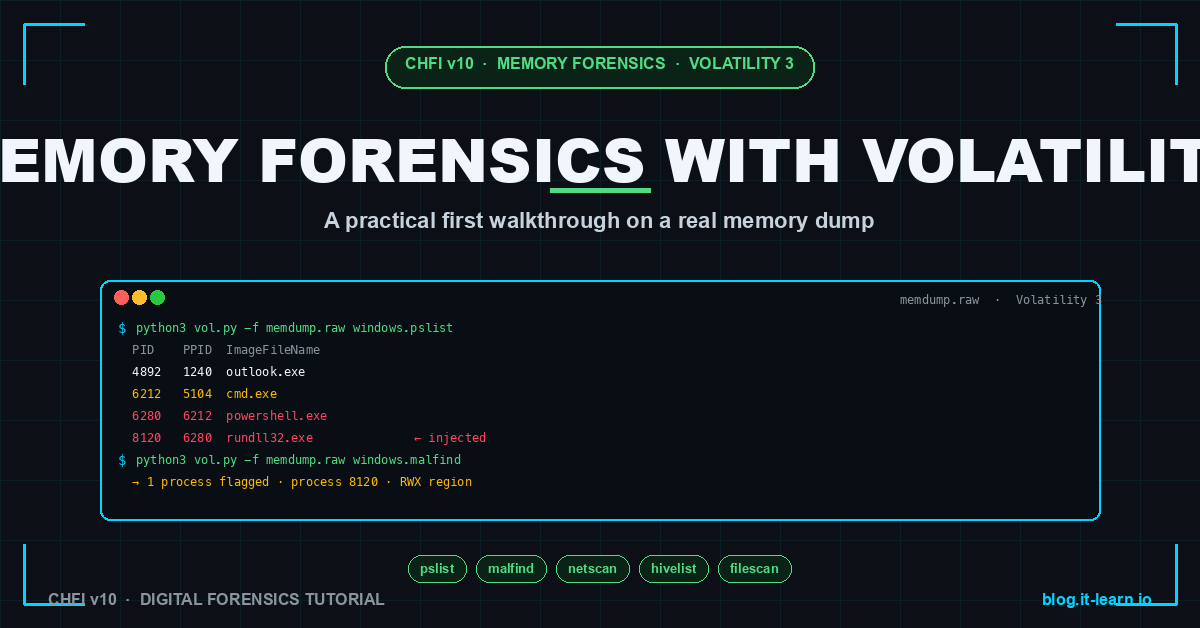
Memory forensics with Volatility 3 — capture, profile selection, pslist, malfind, netscan, hivelist, and a 30-minute first-investigation walkthrough.
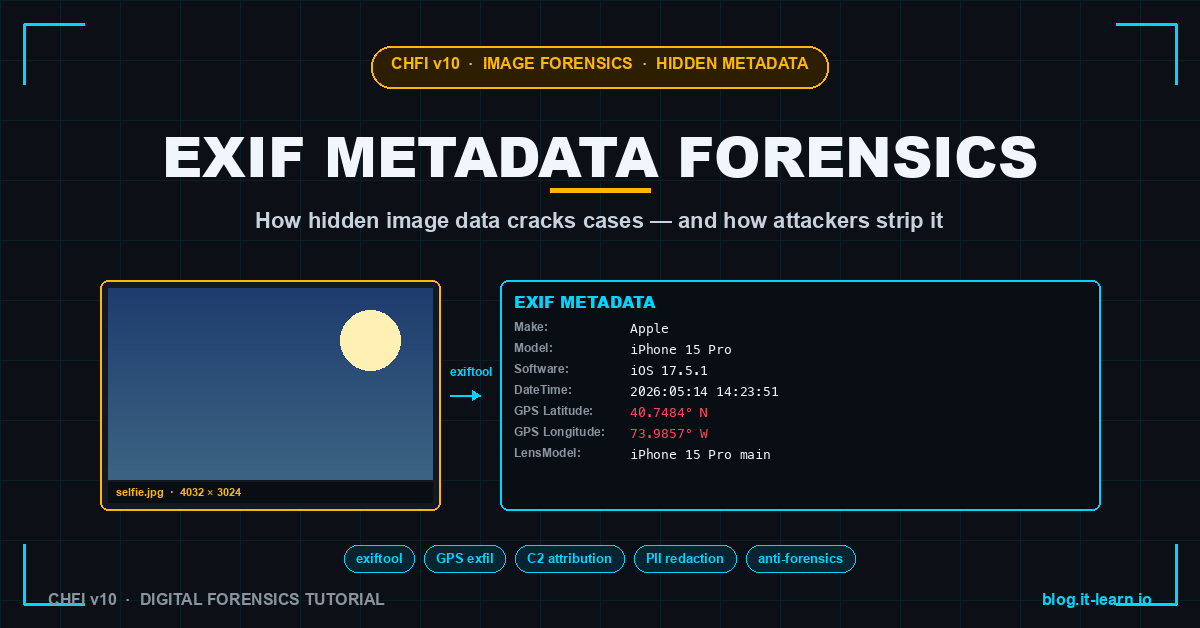
EXIF metadata for forensic examiners — GPS coordinates, camera serial, software signature, real-case examples, and how attackers strip it.

CVE-2026-41089 Windows Netlogon RCE exploited in the wild. Oracle WebLogic CVE-2024-21182 active. Red Hat npm supply chain attack hits 32 packages.

CVE-2026-0257 PAN-OS auth bypass exploited 4 days post-disclosure. Microsoft MFA outage blocks enrollments. 19-year Linux kernel root flaw goes public.
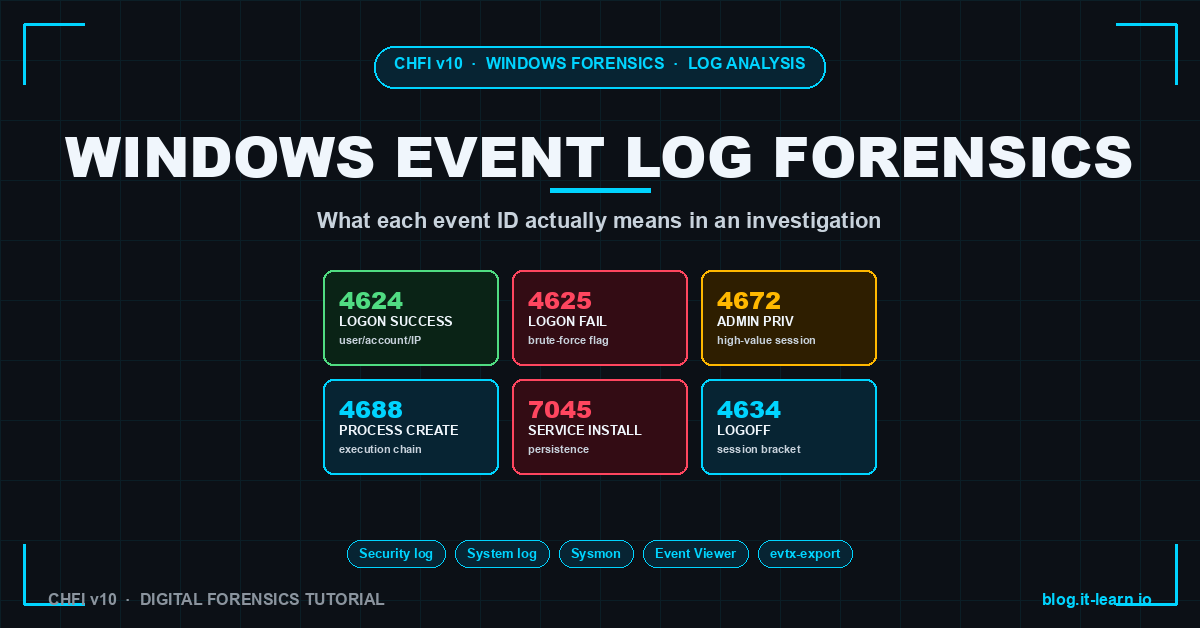
Windows event log forensics decoded — 4624, 4625, 4672, 4688, 4634, 7045, 1102 and how to read them in an investigation.
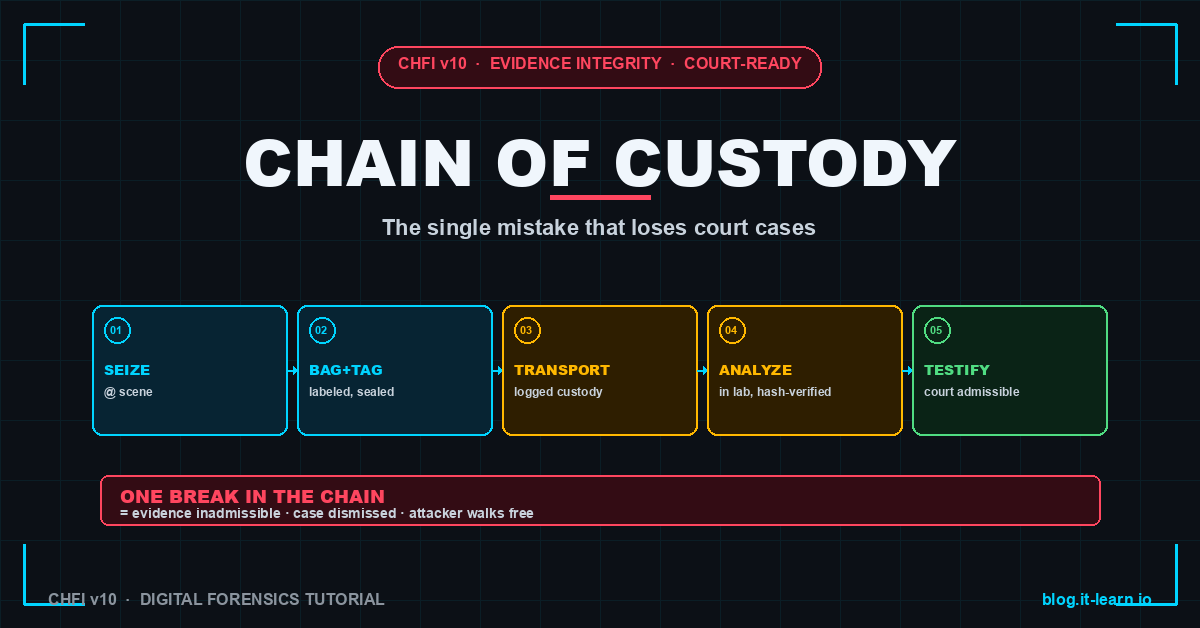
Chain of custody in digital forensics — what to document, the seven failure modes that get evidence thrown out, and the form fields a court actually requires.
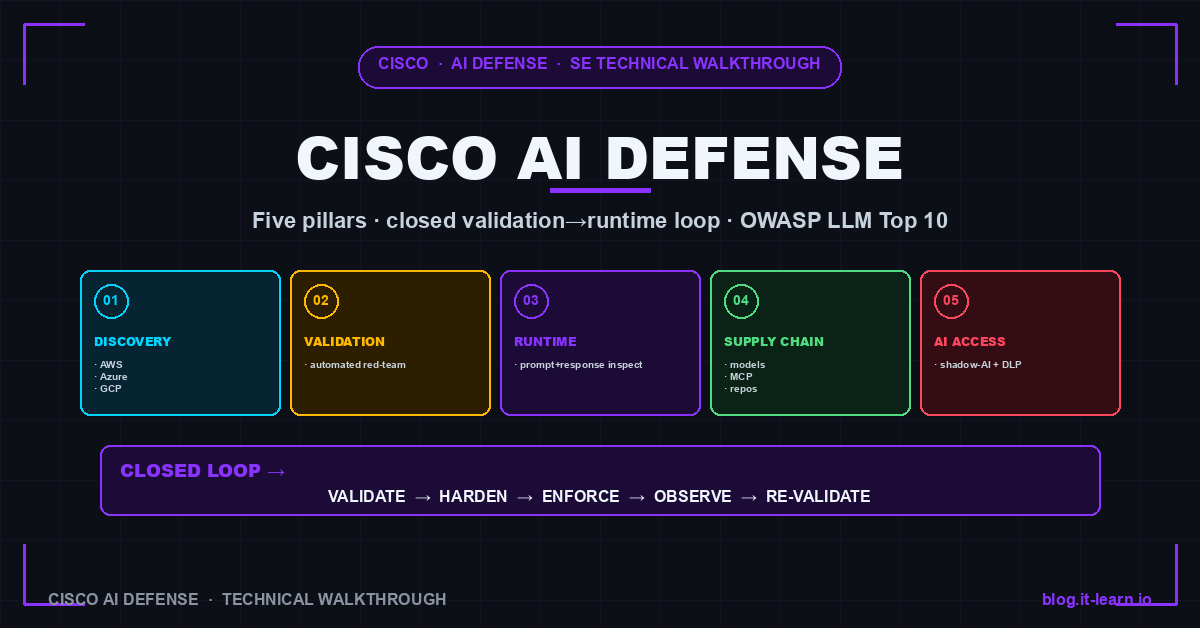
Cisco AI Defense secures the AI lifecycle — discovery, validation, runtime protection, supply chain, and shadow-AI control. A solutions engineer's deep …
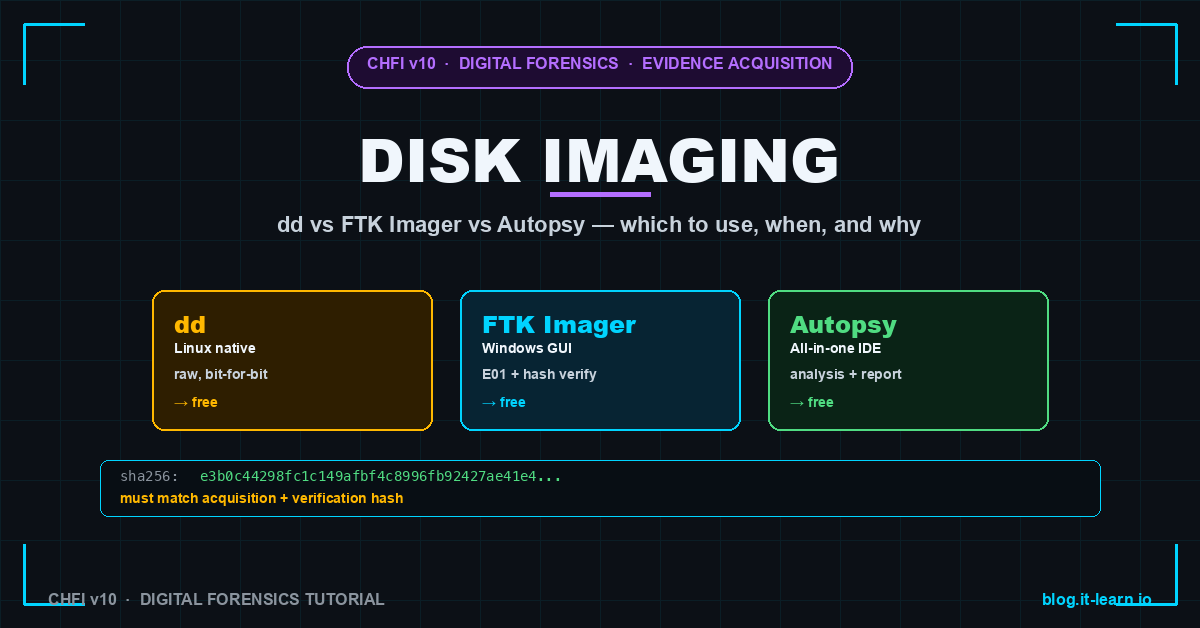
Forensic disk imaging compared — dd, FTK Imager, and Autopsy. When to use each, write-blocker requirements, hash verification, and court-admissible output.
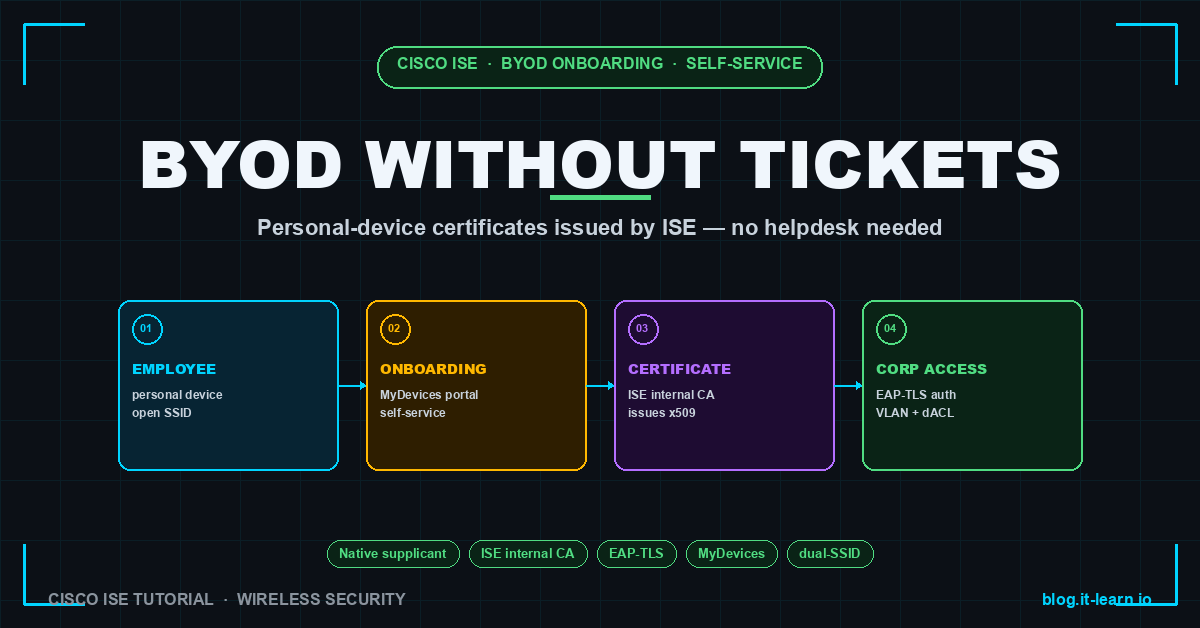
Complete Cisco ISE BYOD onboarding guide — dual-SSID flow, internal CA, native supplicant provisioning, MyDevices portal, and lifecycle management.

CVE-2026-0263 and CVE-2026-0264 deliver RCE in PAN-OS VPN and DNS processing. FortiClient EMS CVE-2026-35616 exploited in the wild.

ShinyHunters breach Carnival for 5.9M records. Google unifies Mandiant, Wiz, and Gemini. JINX-0164 deploys macOS backdoors against crypto firms.
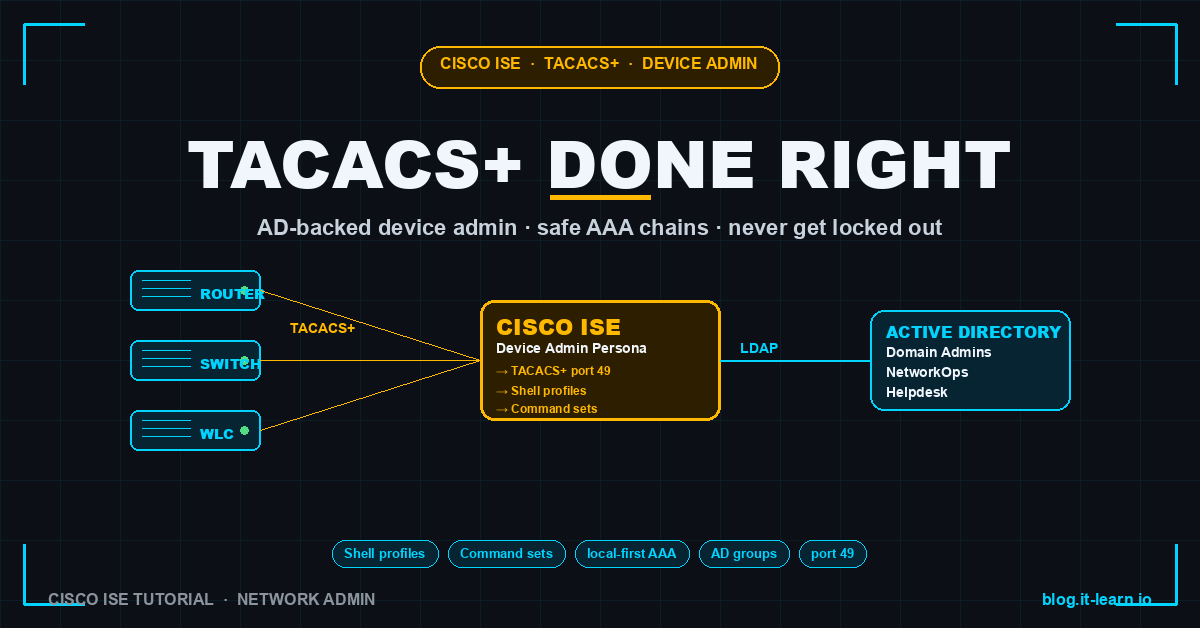
Complete Cisco ISE TACACS+ device admin guide — Device Admin persona, shell profiles, command sets, AD integration, and the safe AAA chain pattern.
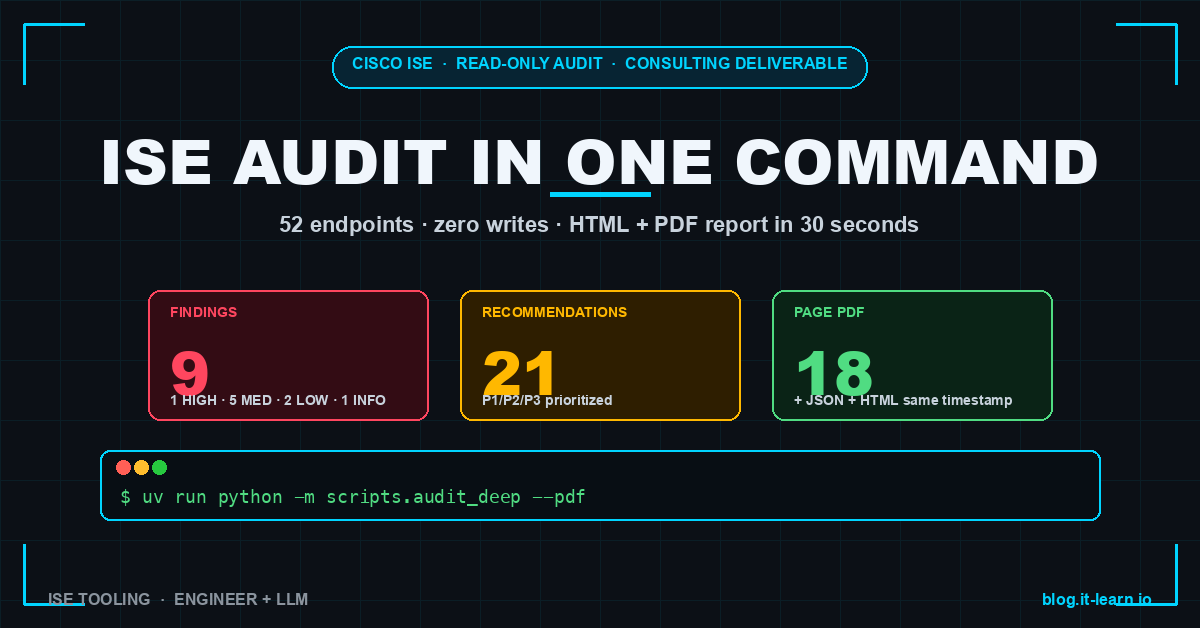
Read-only Cisco ISE audit tool — 52 ERS / OpenAPI endpoints, 9 findings, 21 recommendations, HTML + PDF report in 30 seconds. Open source on GitHub.
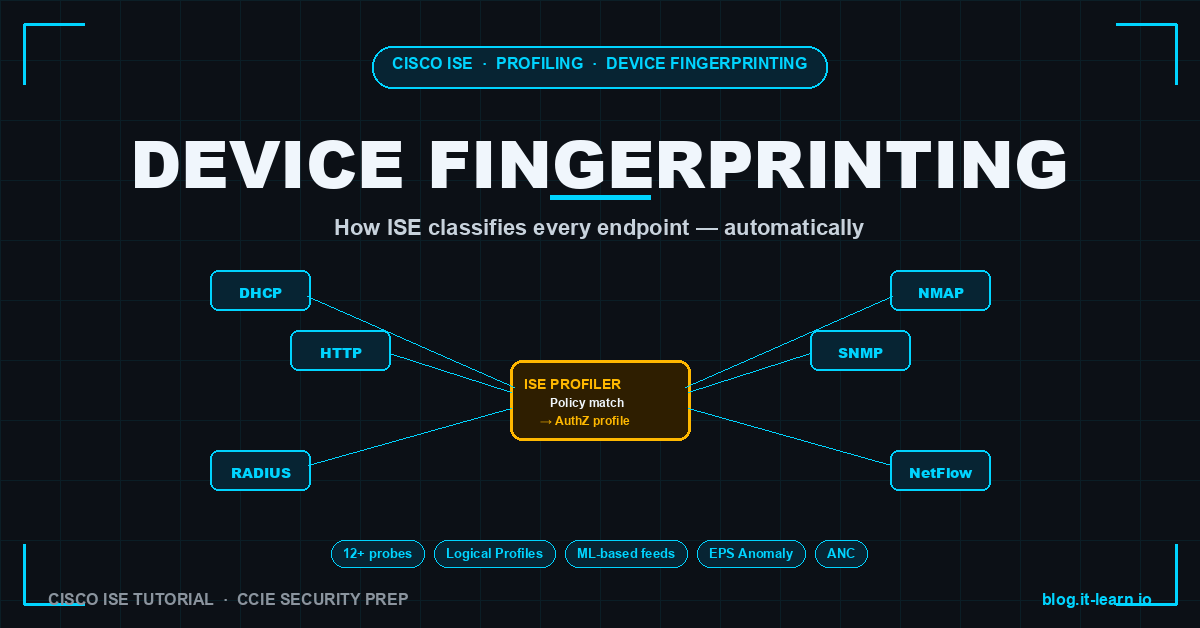
How Cisco ISE Profiling classifies every endpoint automatically — probes, policy hierarchy, Certainty Factor, configuration walkthrough, and the gotchas.

FBI flash alert on Silent Ransom Group USB attacks at law firms. LA Metro attributed to Iranian APT. SymJack weaponizes AI coding agents. CVE-2026-45659.

CISA orders 48-hour Drupal patching for active SQLi exploitation, Dutch police seize 800 bulletproof hosting servers, Iran APT hits aviation sector.

Megalodon injects malicious workflows into 5,500+ GitHub repos, CVE-2026-26980 Ghost CMS zero-day exploited, TrapDoor plants 34 packages on npm and PyPI.

Ubiquiti patches three CVSS 10.0 UniFi OS RCEs, nation-state actors weaponize ROADtools for Azure AD recon, Apex One zero-day CVE-2026-34926 hits KEV.
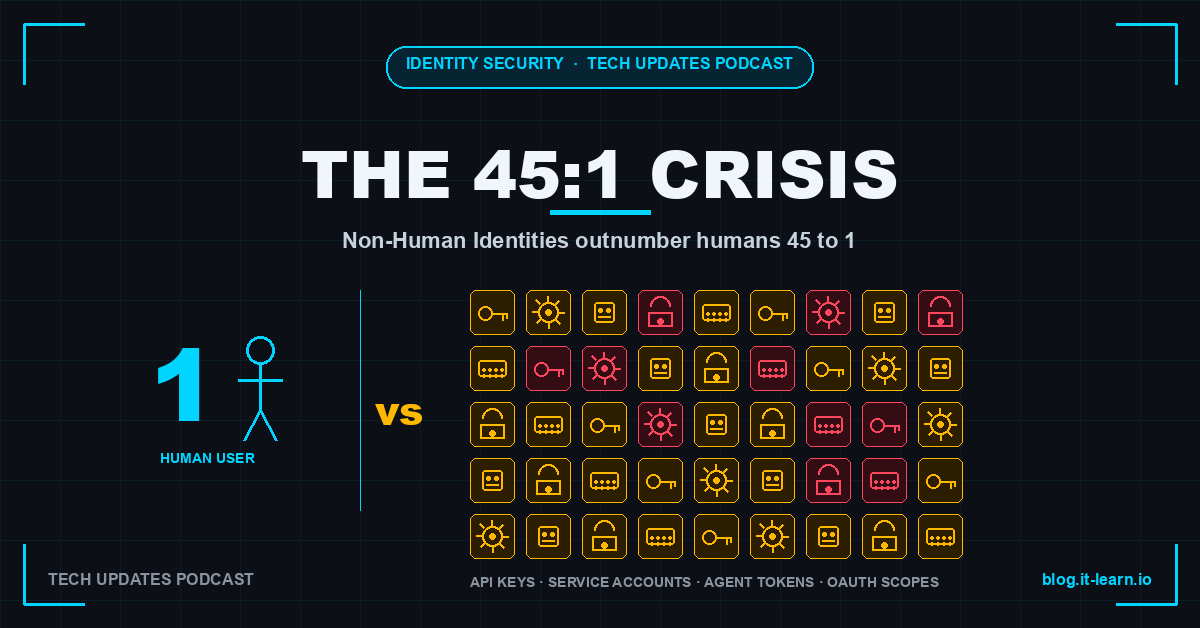
45 to 1. In the average enterprise, for every human user there are 45 machine identities. Every API key. Every service account. Every agent token. Every secret