How to Build a Business Case for NAC (Network Access Control)
Build a compelling NAC business case with ROI frameworks, cost models, and a 3-slide executive template. Align CISO and CFO priorities for Cisco ISE and NAC …
Posts
Build a compelling NAC business case with ROI frameworks, cost models, and a 3-slide executive template. Align CISO and CFO priorities for Cisco ISE and NAC …
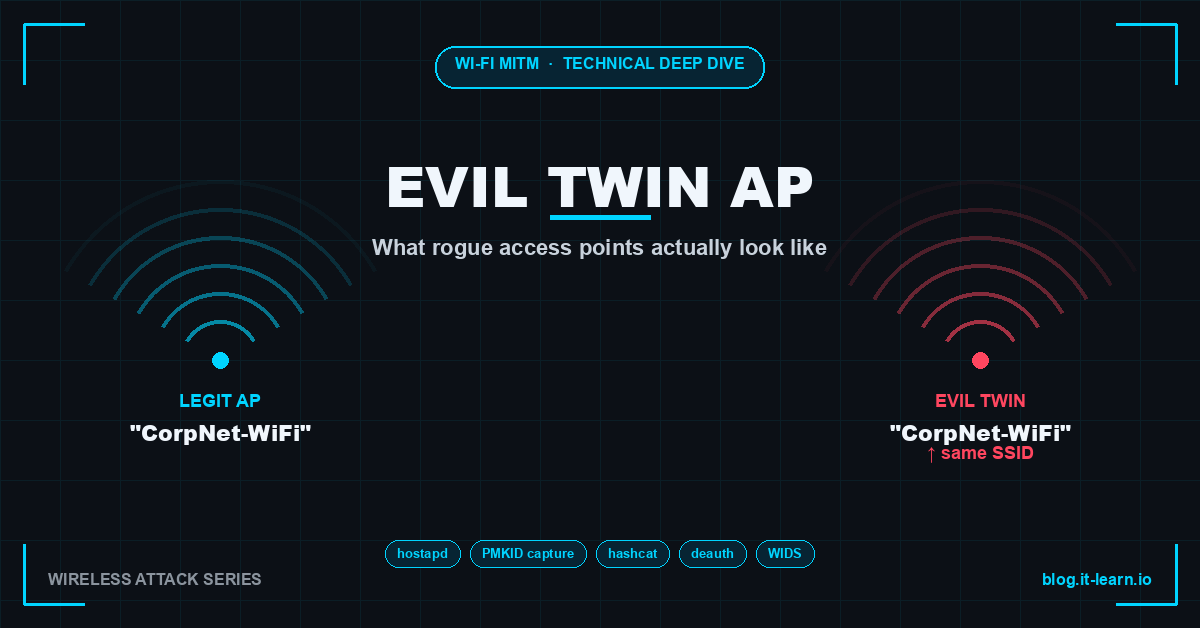
Technical deep dive into Evil Twin AP attacks: hostapd setup, PMKID capture, WPA2 cracking with hashcat, deauth floods, and enterprise WIDS defenses.

ShinyHunters breaches ADT (5.5M) and Medtronic (9M records). CVE-2026-32202 Windows Shell flaw exploited in the wild. UNC6692 Teams malware campaign.
Five proven AD persistence techniques — Golden Ticket, Silver Ticket, DCSync, AdminSDHolder, and Skeleton Key — with Mimikatz commands, Event IDs, BloodHound …

Pack2TheRoot race condition grants root on RHEL/Ubuntu/Fedora. Itron SCADA vendor breached. US sanctions cyberscam compounds.
50 essential cybersecurity terms every account manager needs to know. Definitions, why customers care, and what to say in meetings. Organized by category.
Learn how to read pen test reports, map findings to solutions, and build remediation roadmaps that drive cybersecurity sales without using scare tactics.

How SIM swap attacks work, real cases including Jack Dorsey and FTX, detection signals, and defenses — carrier PINs, port freeze, and moving beyond SMS MFA.

Master the 5 most common security objections in pre-sales. Rebuttal frameworks, real breach examples, and talk tracks for solutions engineers and sales teams.
OAuth 2.0 attack vectors — device code phishing, open redirects, illicit consent grants — with curl examples, Microsoft Graph detection queries, and defense …