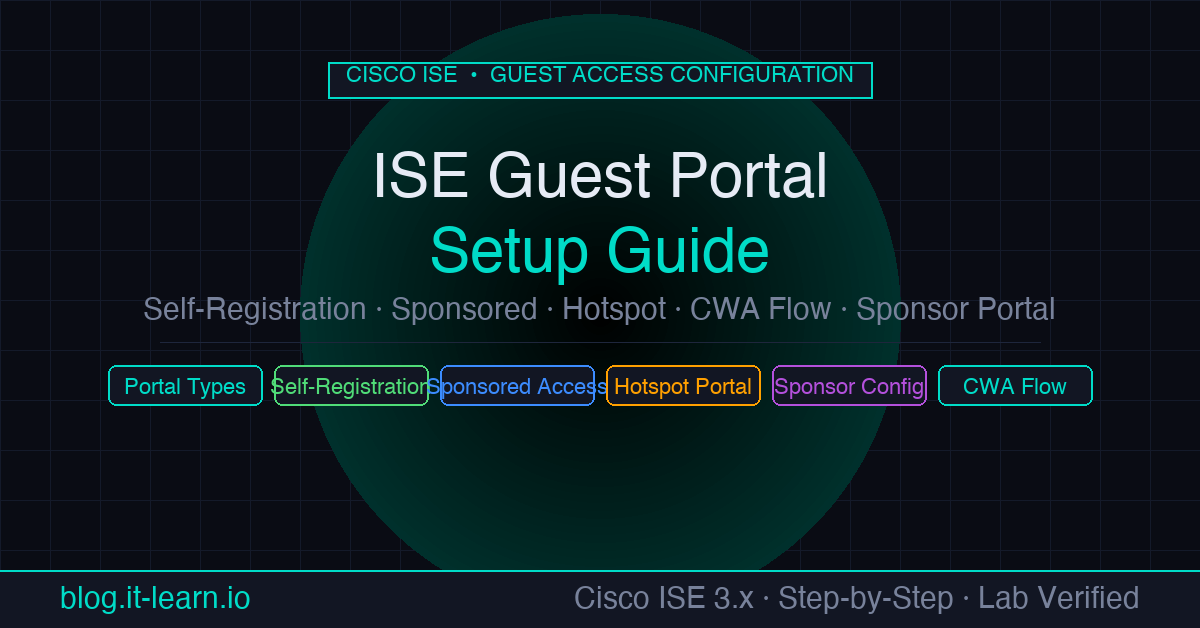
ISE’s guest access system is one of its most visible features — visitors, contractors, and BYOD users all need network access, and ISE gives you complete control over how that access is granted, monitored, and expired. But the configuration has a lot of moving pieces: portal types, sponsor workflows, CWA redirects, guest types, and VLAN assignments all need to work together.
This guide walks through the full setup for all three portal types, the CWA flow that ties it to the network, and the sponsor portal configuration for enterprise deployments.
How ISE Guest Access Works
Before touching configuration, understand the flow:
- An unregistered device connects to the guest SSID or VLAN
- The network device (switch/WLC/Meraki) runs MAC Authentication Bypass (MAB) — it sends the device MAC to ISE
- ISE doesn’t recognize the MAC and returns an authorization result that redirects the browser to the guest portal
- The device’s browser opens any HTTP page and gets redirected to the ISE portal URL
- The guest registers, logs in, or accepts the AUP depending on portal type
- ISE sends a Change of Authorization (CoA) back to the network device
- The network device re-authenticates the session and grants guest network access
This is Central Web Authentication (CWA) — the portal lives on ISE, not on the network device.
Portal Type 1 — Self-Registered Guest Portal
Best for: public events, open coworking spaces, visitor lobbies — anywhere guests can self-serve without needing a sponsor.
Create the Portal
- Go to Work Centers > Guest Access > Portals & Components > Guest Portals
- Click Create and select Self-Registered Guest Portal
- Set a name (e.g.
Self-Reg-Guest-Portal) - Configure Portal Settings:
- HTTPS Port: leave at 8443 (or your chosen port)
- Allowed Interfaces: select the ISE PSN interface guests will hit
- Certificate: select a certificate trusted by guest browsers (or a public CA cert)
Portal Behavior Settings
Under the Self-Registration tab:
- Fields to collect: at minimum, First Name, Last Name, and Email Address
- Require email verification: sends a confirmation link — good for accountability, adds friction
- Require admin approval: holds the account pending sponsor approval before access is granted
- Guest Type: assign the guest type that controls account duration and access level (configure guest types first — see below)
- AUP: enable and paste your acceptable use policy text
Guest Types
Guest Types control how long accounts last and what kind of access guests receive.
- Go to Work Centers > Guest Access > Portals & Components > Guest Types
- Edit or create a Guest Type:
- Maximum Account Duration: e.g.
1 Day - Allow guests to extend their access: optional
- Login options: simultaneous logins, maximum failed login attempts
- Maximum Account Duration: e.g.
- Assign this Guest Type to the portal
Portal Type 2 — Sponsored Guest Portal
Best for: enterprise visitors, contractors, auditors — anyone who needs access granted by an internal employee.
The sponsor (employee) creates the guest account via the Sponsor Portal. The guest receives credentials by email or SMS and logs in through the guest portal.
Create the Guest Portal
Same as above but choose Sponsored Guest Portal. The login page will ask for username/password — credentials the sponsor provides.
Configure the Sponsor Portal
Go to Work Centers > Guest Access > Portals & Components > Sponsor Portals
Edit the default
Sponsor Portalor create a new oneUnder Sponsor Groups tab, configure which internal users can be sponsors:
- Map an AD group (e.g.
corp.example.com/Groups/Guest-Sponsors) to theALL_ACCOUNTSsponsor group - Or use ISE internal groups if not using AD
- Map an AD group (e.g.
Under the sponsor group permissions, configure:
- What guest types can sponsors create: restrict sponsors to specific guest types (e.g. 1-day visitor accounts only)
- Can sponsors approve accounts: set if sponsor-approved accounts need manual activation
- Can sponsors delete guests: yes for self-serve management
- Can sponsors extend accounts: optional
Sponsor Workflow
Once configured, sponsors log in to https://<ise-psn>:8443/sponsorportal using their AD credentials. They can:
- Create a guest account (enter name, email, duration)
- Print or email the credentials to the guest
- View all active guest sessions they’ve created
- Extend or revoke access
Portal Type 3 — Hotspot Portal
Best for: cafeterias, waiting rooms, hotel lobbies — maximum convenience, minimum friction.
Guests connect, open a browser, see an AUP page, click Accept, and get access. No credentials. ISE registers the MAC address and grants access automatically.
- Go to Work Centers > Guest Access > Portals & Components > Guest Portals
- Create a Hotspot Guest Portal
- Configure the AUP text and optional redirect URL after acceptance
- Optionally enable Require guest device compliance if you want to redirect non-compliant devices
Hotspot portals use a pre-auth access code (optional) — if enabled, you post a code in the room and guests enter it to proceed past the AUP. Useful for filtering unauthorized access in physical spaces.
Configuring the CWA Redirect Flow
This is the ISE policy configuration that ties the portal to your network.
Step 1 — Create a Redirect ACL
On your network device, create an ACL that:
- Permits DNS (UDP 53) and DHCP (UDP 67/68) — needed before the guest can reach the portal
- Permits traffic to ISE PSN IP (so the portal redirect works)
- Denies everything else
For Cisco Catalyst switches:
ip access-list extended GUEST_REDIRECT
permit udp any any eq 53
permit udp any any eq 67
permit udp any any eq 68
permit tcp any host <ISE-PSN-IP> eq 8443
deny ip any any
For Meraki: create a Group Policy with a firewall rule. Meraki handles the redirect internally without a named ACL.
Step 2 — Create the Guest Authorization Profile
- Policy > Policy Elements > Results > Authorization > Authorization Profiles
- Create profile:
Guest_CWA_Redirect - Set Web Redirection type to
Centralized Web Auth - Select the guest portal you created
- Set ACL to the redirect ACL name above
- Leave VLAN blank — the guest VLAN assignment happens after CoA
Step 3 — Create a Post-Authentication Authorization Profile
After the guest authenticates through the portal:
- Create profile:
Guest_Access - Set VLAN to your guest VLAN ID (e.g. VLAN 100)
- Set a downloadable ACL (dACL) limiting guest access — typically allow internet, deny RFC1918 (internal networks)
Step 4 — Build the Authorization Policy Rules
In your policy set, add two rules in this order:
| Priority | Condition | Result |
|---|---|---|
| 1 | Network Access:UseCase EQUALS Guest Flow AND Session:PortalName EQUALS Self-Reg-Guest-Portal | Guest_Access |
| 2 | Radius:Called-Station-ID ENDS_WITH :Guest-SSID OR Network Access:AuthenticationMethod EQUALS MAB | Guest_CWA_Redirect |
Rule 2 catches the initial unauthenticated MAB and serves the redirect. Rule 1 (evaluated first) catches the post-portal-authentication CoA and grants access.
Email and SMS Notifications
Email Setup
- Administration > System > Settings > SMTP Server
- Enter your SMTP server hostname, port, and credentials
- Test the connection
Once configured, guest portal email notifications will work automatically for self-registered and sponsored accounts.
SMS Setup
- Work Centers > Guest Access > Settings > SMS Gateway
- Select your SMS gateway provider (Clickatell, Syniverse, or custom HTTP)
- Enter API credentials
- Map the provider format to ISE’s notification template
Verifying Guest Sessions
After a guest authenticates:
- Operations > RADIUS > Live Logs — confirm the MAB authentication and CoA re-authentication appear
- Work Centers > Guest Access > Reports > Guest Activity — shows all active guest sessions, account status, and login history
- Operations > Reports > Guest > Master Guest Report — audit trail of all guest accounts created, activated, and expired
Common Issues
Guest is redirected but portal page won’t load
- Check firewall between client and ISE PSN on port 8443
- Verify the ISE portal certificate is trusted by the guest browser (use a public CA cert for public-facing portals)
- Confirm the redirect ACL permits traffic to the ISE PSN IP
CoA after portal login doesn’t work — guest stays on redirect ACL
- Confirm CoA is enabled on the NAD:
aaa server radius dynamic-authoron Catalyst, or CoA enabled in Meraki RADIUS settings - Verify CoA port 1700 is open from ISE to the NAD
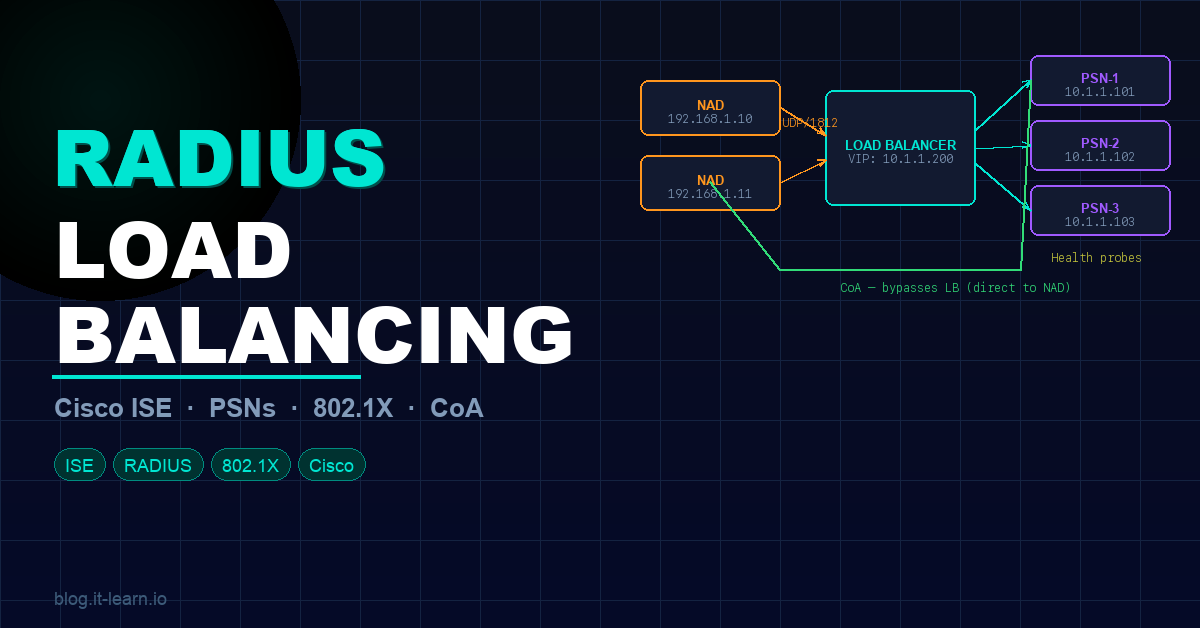
- Check that the NAD is using the real PSN IP for CoA, not the load balancer VIP
Sponsor can’t create guest accounts
- Verify the sponsor’s AD group is mapped to a Sponsor Group in ISE
- Confirm the sponsor is authenticating with AD credentials (not local ISE account)
- Check that the Sponsor Portal is reachable at
https://<ise-psn>:8443/sponsorportal
Practice with free flashcards, quizzes, and hands-on lab scenarios at cciesec.it-learn.io — built specifically for the CCIE Security v6.1 written (350-701 SCOR) and lab exam.
Related ISE Content
- Cisco ISE Active Directory Integration — prerequisite: join ISE to AD before configuring AD-based sponsor groups
- How to Integrate Meraki with Cisco ISE — configure Meraki as the NAD for CWA guest flows
- RADIUS Load Balancing for Cisco ISE — distribute guest portal traffic across multiple PSNs