Network access control without posture is trust based on identity alone. Posture adds a second layer: even if you are who you say you are, is your device actually secure? ISE posture assessment answers that question — checking antivirus status, patch levels, disk encryption, and more before granting full access.
This guide covers the complete posture configuration: client provisioning, conditions, requirements, policy, compliance state handling, and remediation.
Architecture Overview
Posture in ISE works across three planes:
- Client Provisioning — getting the AnyConnect posture agent onto the endpoint
- Posture Policy — defining what the endpoint must pass
- Authorization Policy — acting on the compliance state (compliant → full access, non-compliant → quarantine)
The posture check is run by the AnyConnect ISE Posture module on the endpoint. It communicates with ISE over HTTPS (port 8905 or 443). ISE tells the agent what to check, the agent runs the checks, reports back, and ISE updates the session’s posture status attribute — which authorization policy then acts on.
Prerequisites
Before configuring posture:
- ISE must already be joined to Active Directory (or have internal users) — posture requires an authenticated identity to apply policy
- AnyConnect licenses must be applied to ISE (Apex or Premier tier includes posture)
- The AnyConnect package must be uploaded to ISE: Policy > Policy Elements > Results > Client Provisioning > Resources — upload the
.pkgfile downloaded from Cisco.com - Firewall must allow TCP 8905 from client to ISE PSN (posture keepalive port), plus TCP 443
Step 1 — Upload AnyConnect and Create a Posture Profile
Upload the AnyConnect Package
- Policy > Policy Elements > Results > Client Provisioning > Resources
- Click Add > Agent Resources from Local Disk
- Upload the AnyConnect package (e.g.
anyconnect-win-4.10.x.pkg) - ISE will extract the available modules — confirm the ISE Posture module is available
Create an AnyConnect Configuration
- Still in Resources, click Add > AnyConnect Configuration
- Select the AnyConnect package
- Under Compliance Module, select the latest compliance module package
- Name it (e.g.
AC-Posture-Win) and save
Create a Posture Profile
The posture profile tells the agent where to find ISE for check-in:
- Policy > Policy Elements > Results > Client Provisioning > Resources > Add > AnyConnect Posture Profile
- Set Server name rules to
*.yourdomain.com(or the ISE FQDN) - Set Discovery host to the ISE PSN FQDN
- Save
Step 2 — Configure Client Provisioning Policy
The client provisioning policy determines what gets installed on which endpoints:
- Work Centers > Posture > Client Provisioning > Client Provisioning Policy
- Add rules, for example:
| Rule Name | OS | Result |
|---|---|---|
| Windows-Provisioning | Windows All | AnyConnect Config: AC-Posture-Win |
| Mac-Provisioning | Mac OS X All | AnyConnect Config: AC-Posture-Mac |
- Ensure the rule for your target OS returns the AnyConnect configuration you created
When an unprovisioned endpoint hits this policy, ISE serves the AnyConnect installer through the provisioning portal.
Step 3 — Create Posture Conditions
Conditions are the individual checks ISE runs on the endpoint. Navigate to Work Centers > Posture > Policy Elements > Conditions.
Common Condition Types
File Condition — check if a file exists or has a specific hash:
- File Path:
C:\Program Files\CrowdStrike\CSFalconService.exe - Operator:
exists
Registry Condition — check a registry key value (Windows only):
- Path:
HKLM:\SOFTWARE\Policies\Microsoft\Windows\WindowsUpdate\AU - Value:
NoAutoUpdate - Operator:
equals 0
Application Condition — check if a process is running or an application is installed:
- Application name:
CrowdStrike Falcon Sensor - Check type:
Running ProcessorInstalled Application
Anti-Malware Condition (most common):
- Condition type:
Anti-Malware - Product: select from the list (CrowdStrike, Defender, McAfee, etc.)
- Check: definition date within last N days
Patch Management Condition:
- Product: Windows Update, WSUS, SCCM
- Check: last update within N days
Disk Encryption Condition:
- Product: BitLocker, FileVault, Symantec Encryption
- Check: encryption enabled
Step 4 — Create Posture Requirements
Requirements group conditions into a single pass/fail check with a remediation action attached.
- Work Centers > Posture > Policy Elements > Requirements
- Click Add
- Set:
- Name: e.g.
Req-AV-UpToDate - Operating System: Windows All
- Conditions: select the Anti-Malware condition you created
- Remediation Action: select
AV-Remediation(or create a custom one)
- Name: e.g.
Remediation Actions — create under Work Centers > Posture > Policy Elements > Remediation Actions:
- For AV updates: select
Anti-Malware Remediation, pick the product - For patch management: select
Patch Management Remediation - For custom scripts: select
Launch Program, specify the executable path
Step 5 — Build Posture Policy
The posture policy maps identity groups and OS types to requirements:
- Work Centers > Posture > Posture Policy
- Add rules:
| Rule | Identity Group | OS | Requirements | Temporal |
|---|---|---|---|---|
| Corp-Windows-Full | Any | Windows All | Req-AV-UpToDate, Req-OS-Patched, Req-Disk-Encrypted | Session |
| Corp-Mac-Basic | Any | Mac OS X All | Req-AV-UpToDate | Session |
| BYOD-Minimal | GuestType_Daily | Windows All | Req-AV-Exists | Session |
- Temporal posture checks run every time the session is established
- Periodic posture re-checks on a timer (configurable under Administration > System > Settings > Posture)
Step 6 — Configure Authorization Policy for Compliance States
This is where posture status becomes network access policy. In Policy > Policy Sets > your policy set > Authorization Policy, add three rules:
Rule 1 — Non-Compliant (evaluate first)
- Condition:
Session:PostureStatus EQUALS NonCompliant - Result:
Quarantine_VLANor a redirect to a remediation page
Rule 2 — Unknown (not yet assessed)
- Condition:
Session:PostureStatus EQUALS Unknown - Result:
Posture_Redirectprofile (redirect to provisioning portal, allow DNS/DHCP)
Rule 3 — Compliant
- Condition:
Session:PostureStatus EQUALS CompliantAND your normal identity conditions - Result:
Full_Accessauthorization profile
Order matters: Non-Compliant must be above Unknown, and both must be above the Compliant + identity rules. Otherwise a compliant user could match the wrong rule.
Create the Posture Redirect Authorization Profile
- Policy > Policy Elements > Results > Authorization > Authorization Profiles
- Create:
Posture_Redirect - Web Redirection:
Client Provisioning (Posture) - ACL: an ACL allowing DNS, DHCP, and ISE PSN traffic only
- Save
Step 7 — Verify End to End
Test Sequence
- Connect a managed endpoint to the network
- Watch Operations > RADIUS > Live Logs — confirm the initial authorization hits the
Unknownposture rule - The browser should be redirected to the provisioning portal
- If AnyConnect is not installed, it prompts for installation
- After AnyConnect installs and the posture check runs, watch Live Logs for a CoA re-authentication
- Confirm the session moves to
Compliantand gets the full access profile
Posture Reports
- Operations > Reports > Endpoints and Users > Posture Assessment by Endpoint — per-endpoint compliance history
- Operations > Reports > Endpoints and Users > Posture Assessment by Requirement — which requirements are failing and on which endpoints
- Work Centers > Posture > Dashboard — real-time compliance posture overview
Troubleshooting
Endpoint stays in Unknown state permanently
- AnyConnect posture module is not installed or not communicating
- Check TCP 8905 is open from client to ISE PSN
- Check
Operations > Troubleshoot > Diagnostic Tools > TCP Dumpon the PSN for inbound posture traffic
Posture check passes in AnyConnect but ISE shows Non-Compliant
- Mismatch between posture profile server name and the ISE PSN the agent is talking to
- Clock skew between client and ISE — posture uses time-stamped tokens
- Check the posture log on the client:
C:\ProgramData\Cisco\Cisco AnyConnect Secure Mobility Client\ISEPosture
AnyConnect provisioning portal shows “unsupported browser”
- Java is required for the legacy provisioning method; use the native Network Setup Assistant instead (configure in client provisioning policy to use the native installer)
- Ensure the endpoint can reach ISE on port 8443
Practice with free flashcards, quizzes, and hands-on lab scenarios at cciesec.it-learn.io — built specifically for the CCIE Security v6.1 written (350-701 SCOR) and lab exam.
Related ISE Content
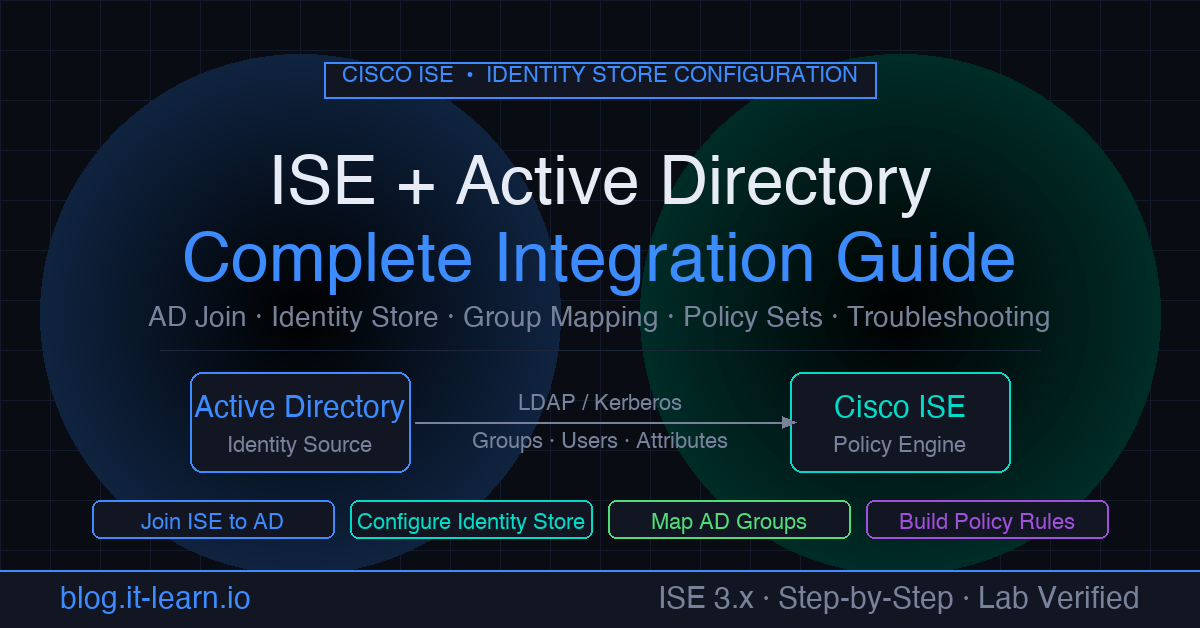
- Cisco ISE Active Directory Integration — required foundation: AD identity before posture policy can reference identity groups
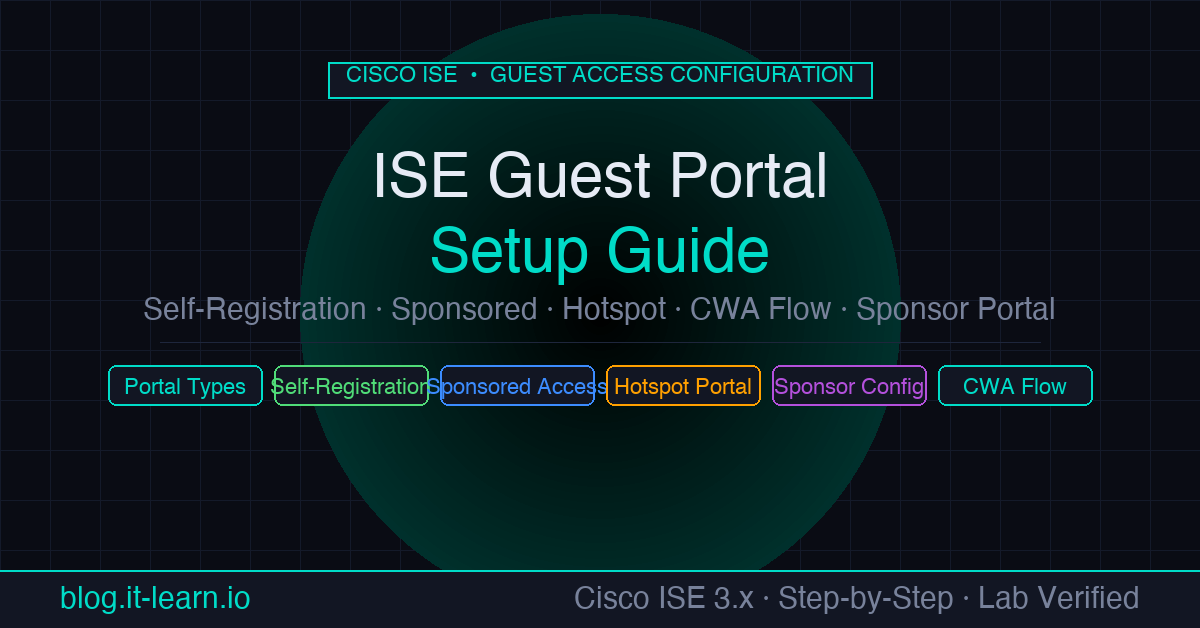
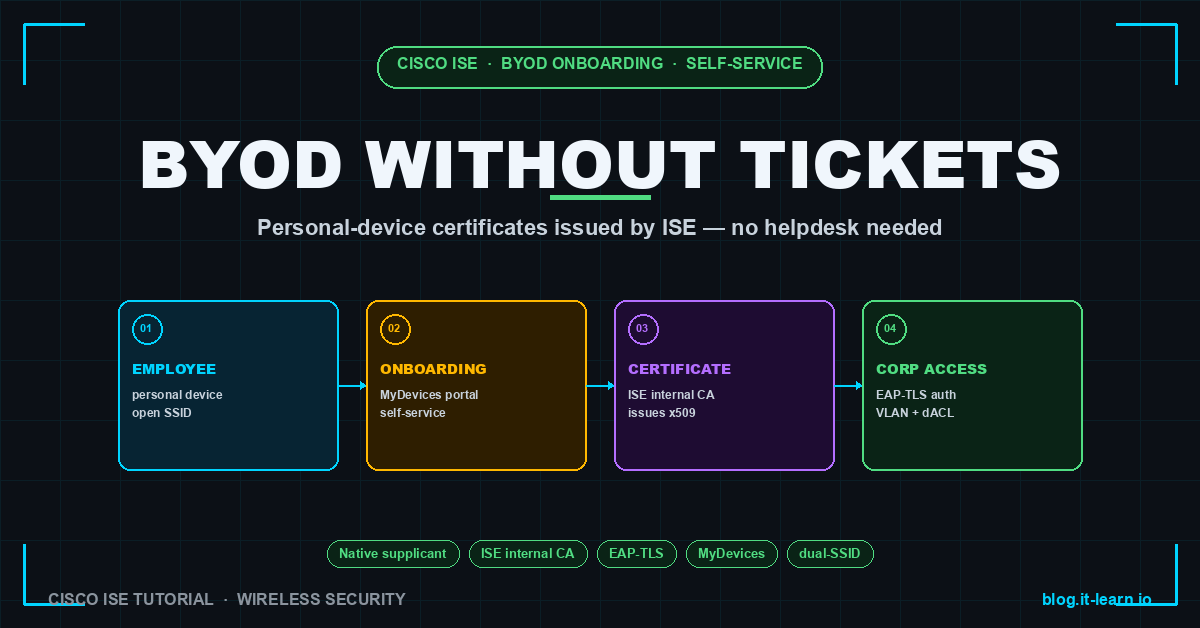
- Cisco ISE Guest Portal Setup — configure guest access alongside posture for BYOD and visitor flows
- How to Integrate Meraki with Cisco ISE — use Meraki as the NAD for posture-based access control