Every customer conversation about security eventually lands on the same question: “What attacks does your solution actually stop?” If you cannot walk through the kill chain of a ransomware double-extortion campaign, explain how a Golden Ticket forges Kerberos credentials, or describe why BGP hijacking can reroute traffic across continents, you lose credibility fast.
This series covers 30 attacks that matter in 2026. Each post breaks down the attack mechanics, maps techniques to the MITRE ATT&CK framework, provides detection queries you can run in Splunk or Sentinel, and outlines concrete defense strategies. These are the attacks you will hear about in security briefings, encounter in RFP responses, and need to demo against in proof-of-concept engagements.
The series runs daily from April 8 through May 7, 2026. Posts are grouped into six categories so you can focus on the domain most relevant to your next customer conversation.
Ransomware & Initial Access
The attacks that get organizations breached in the first place — from trojanized software updates to phishing campaigns that bypass email gateways.
- Supply Chain Attack: How SolarWinds Compromised 18,000 Organizations — How a single poisoned update created the largest espionage campaign in history
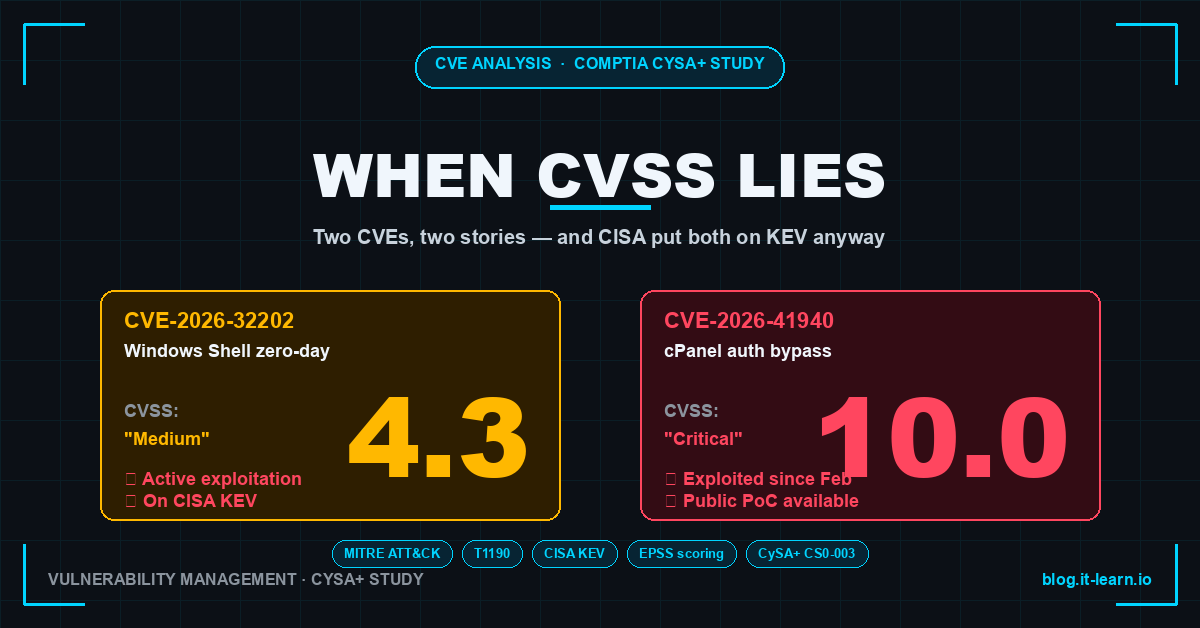
- Zero-Day Exploit: The Patch Doesn’t Exist Yet — Now What? — Understanding the vulnerability window that defenders cannot close
- Ransomware Double Extortion: They Encrypt AND Leak Your Data — How modern ransomware gangs combine encryption with data theft for maximum pressure
- Ransomware, Viruses & Malware Types: Detection Guide — Mapping the major malware families to detection and defense controls
- Living Off the Land: How Attackers Use PowerShell, WMI, and Your Own Tools — Why PowerShell, WMI, and built-in OS utilities are the attacker’s best friends
- Adobe Reader Zero-Day Exploited for Months Before Emergency Patch — A real-world zero-day that lived in the wild long before Adobe shipped a fix
- Watering Hole Attack: They Compromised the Site You Trust — Targeted attacks that weaponize the websites your industry visits every day
- Firmware Rootkit: The Malware That Survives a Full OS Reinstall — Persistence below the operating system that survives reimaging
Network & Protocol Attacks
Attacks that exploit the fundamental protocols holding the internet and enterprise networks together.
- DNS Hijacking: Redirecting Your Traffic Without You Knowing — How attackers poison DNS to intercept traffic before it reaches the real destination
- BGP Hijacking: How Attackers Reroute the Internet Itself — The trust-based routing protocol that lets nation-states redirect entire prefixes
- VLAN Hopping: Jumping Between Network Segments You Shouldn’t Access — Why trunking misconfigurations let attackers jump between network segments
- SSL Stripping: Downgrading HTTPS to HTTP Without the User Noticing — Forcing HTTPS connections back to plaintext without triggering browser warnings
- ARP Poisoning: Intercepting Traffic on Your Own Network — Layer 2 attacks that give adversaries a front-row seat to your internal traffic
Cloud & Infrastructure
Attacks targeting the cloud services, containers, and serverless platforms that run modern applications.
- S3 Bucket Breach: One Misconfigured Permission, Millions of Records Leaked — How a single IAM policy mistake exposes millions of records to the public internet
- Container Escape: Breaking Out of Docker Into the Host — Exploiting container runtimes to gain root access on the underlying host
- Kubernetes RBAC Bypass: When Least Privilege Isn’t Actually Configured — Misconfigured RBAC and service accounts that hand attackers the keys to the cluster
- Cloud Account Takeover: From Leaked AWS Keys to Crypto Mining in 4 Minutes — How fast attackers turn an exposed key into running cryptominers and lateral movement
- Serverless Injection: Attacking Lambda Functions Through Event Data — How untrusted event payloads become code execution in function-as-a-service platforms
Identity & Credential Theft
Attacks that steal, forge, or abuse authentication credentials to move laterally and maintain persistence.
- Kerberoasting: Stealing Service Tickets to Crack Passwords Offline — Requesting service tickets and brute-forcing them without triggering account lockouts
- Pass-the-Hash: Why Stealing the Hash Is Just as Good as the Password — How attackers move laterally without ever cracking the password
- Golden Ticket Attack: Forging Kerberos Tickets for Unlimited Domain Access — Compromising the KRBTGT hash to mint unlimited domain access
- MFA Fatigue Attack: Spamming Push Notifications Until You Tap Approve — Bombarding users with authentication prompts until someone taps approve
- SIM Swap Attack: Taking Over Your Phone Number to Bypass MFA — Social engineering telecom carriers to hijack SMS-based MFA
- Active Directory Persistence: 5 Ways Attackers Stay in Your Domain Forever — From AdminSDHolder abuse to DCShadow, the techniques that survive password resets
Wireless & IoT
Attacks against wireless networks, IoT devices, and the physical-digital boundary.
- Man-in-the-Middle on Wi-Fi: What Evil Twin Access Points Actually Look Like — Rogue access points that clone legitimate SSIDs to intercept corporate traffic
- IoT Botnet: Your Smart Cameras Are DDoSing Someone Right Now — How Mirai and its successors turn cameras and routers into weapons
- Bluetooth Exploitation (BlueBorne): No Pairing Needed, No Interaction Required — Exploiting wireless personal area networks to compromise devices without pairing
- Satellite Hacking: The Viasat Attack That Took Out Ukraine’s Internet in 1 Hour — Intercepting and disabling satellite links that critical infrastructure depends on
Emerging Threats
The next generation of attacks leveraging AI, social engineering, and novel vectors.
- Deepfake CEO Fraud: The Voice on the Call Isn’t Your Boss — AI-generated audio and video that bypass human trust to authorize wire transfers
- Prompt Injection: Making AI Do Things It Shouldn’t — Manipulating LLM-based systems to exfiltrate data and execute unintended actions
- QR Code Phishing (Quishing): That Parking Meter QR Code Is Malicious — How quishing bypasses URL filters by hiding the destination in pixels
- Phishing in 2026: From Classic Emails to AI-Enhanced Deepfakes — The evolution of phishing into multi-channel, AI-personalized campaigns
New posts publish daily from April 8 through May 7, 2026. Subscribe to the newsletter or check back each day for the next attack breakdown.
Practice with free flashcards, quizzes, and hands-on lab scenarios at cciesec.it-learn.io — built specifically for the CCIE Security v6.1 written (350-701 SCOR) and lab exam.