🎙️ This post was auto-generated from the Tech Updates podcast episode.
Malware isn’t just “a virus”—it’s a complex ecosystem of weaponized tools designed to damage systems, steal data, and extort organizations. In 2026, the threat landscape is more sophisticated than ever, and understanding the differences between malware types is critical for any IT or security professional. This episode breaks down the major malware categories, how they infiltrate networks, and the multi-layered defense strategies you need to protect your infrastructure.
What This Episode Covers
- The five major malware types: viruses, worms, trojans, ransomware, spyware, rootkits, and botnets
- Real-world case studies: ILOVEYOU, Colonial Pipeline, Pegasus, Mirai, and SolarWinds
- Seven primary infection vectors and how attackers exploit them
- A defense-in-depth framework with seven actionable layers
- Emerging threat trends from 2024–2026, including RaaS and AI-powered malware
- The business impact of malware attacks and why prevention beats recovery
Deep Dive
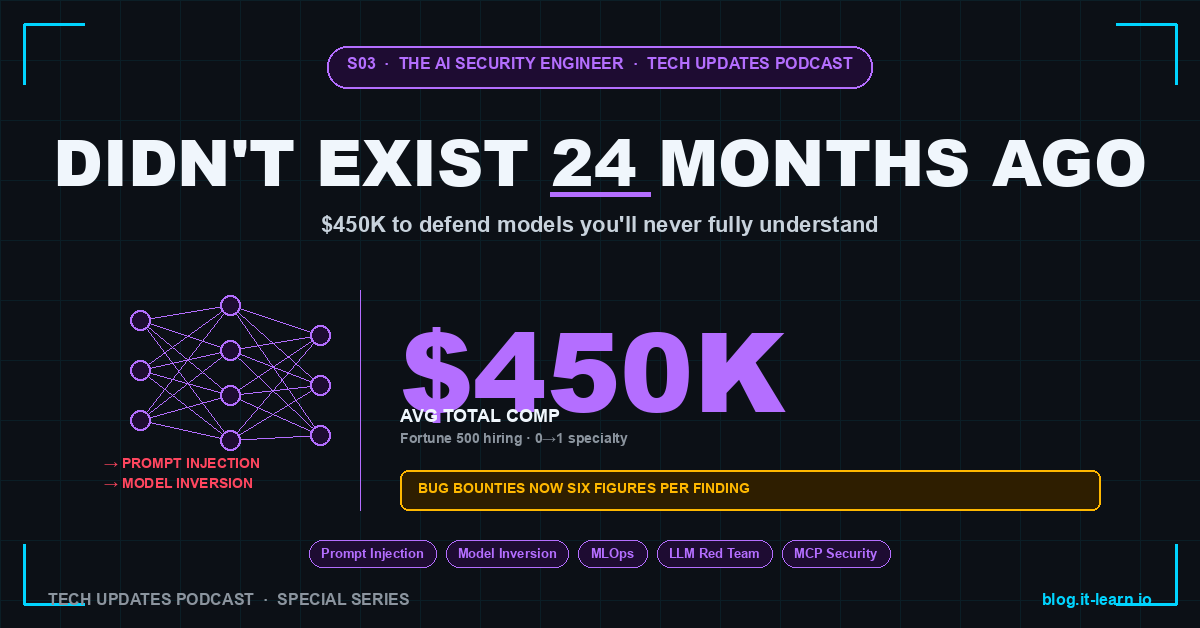
Understanding the Malware Ecosystem
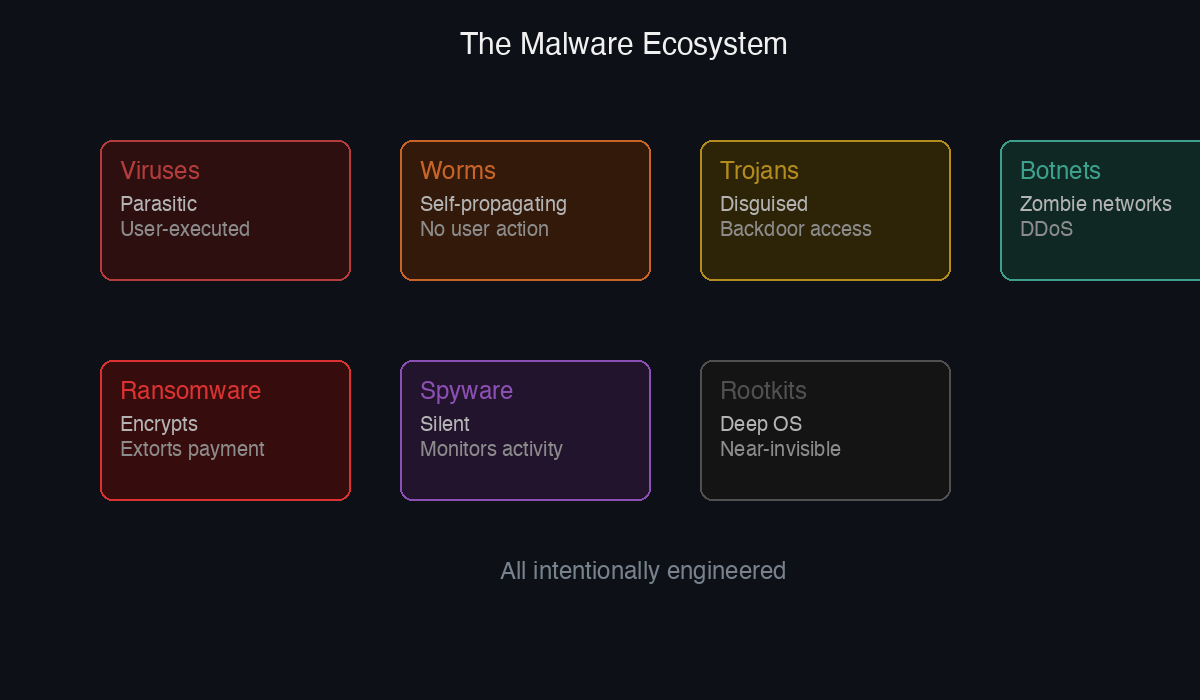
Malware is intentionally engineered—not a bug or accident. The term encompasses any software designed to harm systems, steal data, or enable unauthorized access. The key distinction is intentionality. This matters because it shapes how you defend against it: malware requires different mitigation strategies than accidental vulnerabilities or misconfigurations.
The Five Major Malware Types
Viruses and Worms
Viruses are parasitic: they attach themselves to legitimate files and spread only when a user executes those files. Worms, by contrast, are self-propagating and require no user interaction to spread. The ILOVEYOU worm (2000) infected 50 million machines in just 10 days, demonstrating how quickly self-replicating malware can achieve global impact. Today’s worms often exploit unpatched vulnerabilities to propagate across networks automatically.
Trojans and Ransomware
Trojans disguise themselves as legitimate software—games, utilities, installers—to trick users into execution. Once installed, they can create backdoors, steal credentials, or drop additional payloads. Ransomware represents one of the most financially damaging malware categories: it encrypts your files and demands payment for decryption keys. The Colonial Pipeline attack (2021) resulted in a $4.4 million ransom payment, though this only covered the initial extortion. Double extortion is now standard practice: attackers encrypt your data AND threaten to publish it unless you pay, effectively doubling the pressure on victims.
Spyware and Keyloggers
Spyware operates silently in the background, monitoring user activity, communications, and system behavior without detection. Keyloggers—often delivered as spyware—capture every keystroke, exposing passwords, credit card numbers, and confidential business communications. The Pegasus spyware (developed by NSO Group) exemplifies nation-state capability: it reportedly infected devices through a single missed call, targeting journalists, human rights activists, and world leaders.
Rootkits and Botnets
Rootkits embed themselves deep in the operating system or firmware, granting attackers privileged access. The critical challenge with rootkits is that detection is nearly impossible once installed—the only reliable remediation is a complete OS wipe and reinstall. Botnets turn compromised devices into “zombies” for distributed denial-of-service (DDoS) attacks, spam distribution, and cryptocurrency mining. The Mirai botnet (2016) compromised IoT devices like security cameras and routers, then orchestrated attacks that took offline major services including Twitter, Netflix, Reddit, and Amazon.
How Malware Enters Your Network
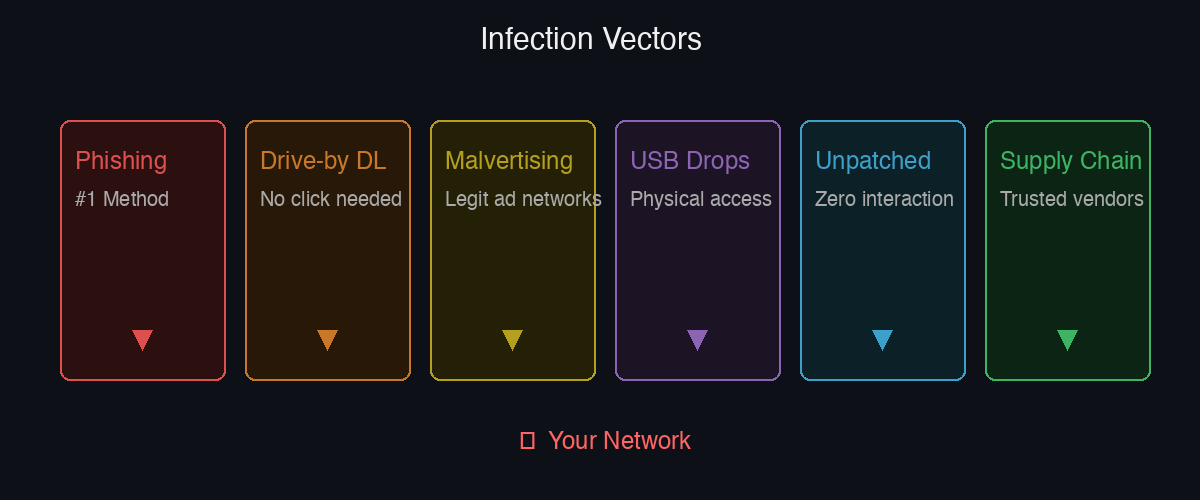
Understanding infection vectors is essential for building effective preventive controls:
- Phishing emails remain the #1 delivery method because they exploit human psychology at scale
- Drive-by downloads silently execute malware when users visit compromised websites—no user action required
- Malvertising injects malicious code into legitimate advertising networks
- USB drops are surprisingly effective: infected drives left in parking lots or public spaces exploit user curiosity
- Unpatched vulnerabilities can be exploited without any user interaction, making patch management critical
- Supply chain attacks like SolarWinds (2020) compromise trusted vendors, affecting 18,000 organizations including US government agencies
Defense-in-Depth: Seven Essential Layers
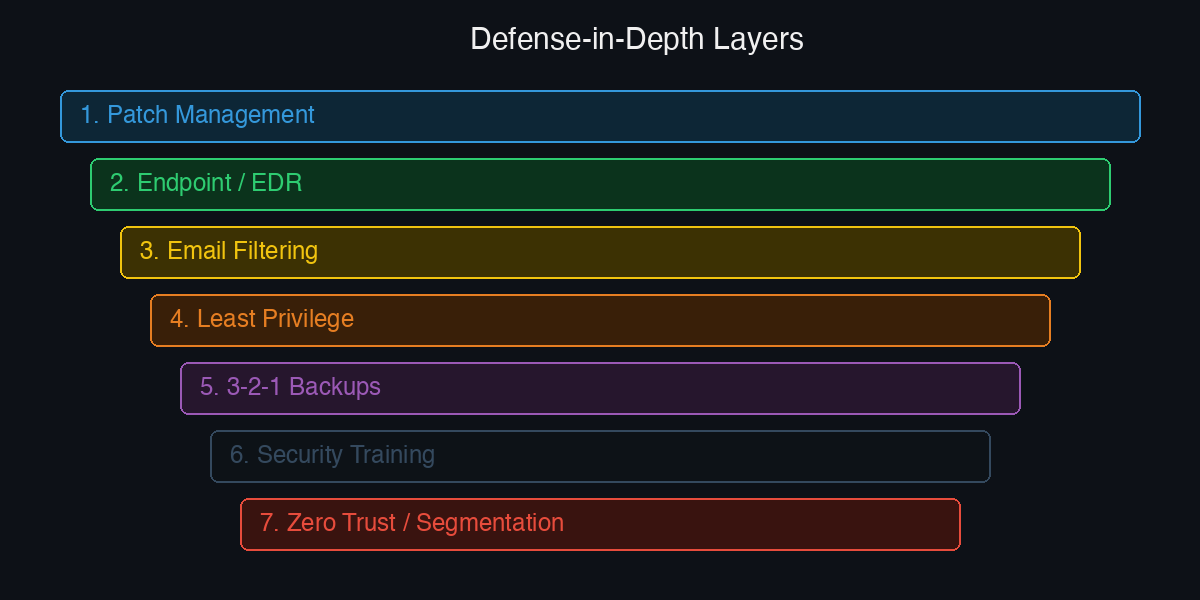
No single tool provides complete protection. Effective malware defense requires layered controls:
- Patch everything — Operating systems, applications, and firmware must be kept current to eliminate known vulnerabilities
- Endpoint protection and EDR — Behavioral detection catches malware variants that signature-based detection misses
- Email filtering and sandboxing — Detonate suspicious attachments in isolated environments before delivery to inboxes
- Least privilege access — Restricts user permissions so compromised accounts limit the blast radius
- 3-2-1 backups — Maintain three copies on two different media types with one copy stored offsite and immutable (preventing ransomware encryption)
- Security awareness training — Human error remains the #1 attack surface; continuous training reduces phishing success rates
- Network segmentation and Zero Trust — Implement “never trust, always verify” principles to contain lateral movement
Emerging Threats in 2024–2026
Ransomware-as-a-Service (RaaS) lowers the barrier to entry for cybercriminals: malware is rented like SaaS subscriptions, requiring no coding expertise. This commoditization has accelerated ransomware attacks globally.
AI-powered malware creates more convincing phishing content and polymorphic variants that adapt in real-time to bypass detection systems. These adaptive threats make static signatures increasingly ineffective.
IoT proliferation expands the attack surface exponentially: billions of smart devices, many running outdated firmware, provide easy footholds for botnet recruitment.
Nation-state malware—Stuxnet, Flame, Triton, Pegasus—demonstrates that government-grade threats are increasingly accessible and widely studied by criminal groups.
The average ransomware attack cost $4.5 million in 2024 (including downtime, recovery, and legal fees). Critically: paying the ransom does NOT guarantee file recovery.
Key Takeaways
- Malware is intentional and engineered—understand the five major types to defend effectively against each
- Phishing emails and unpatched vulnerabilities remain your highest-risk infection vectors
Related Attacks in This Series
- Ransomware Double Extortion: They Encrypt AND Leak Your Data — The encrypt-and-leak combination behind modern ransomware extortion
- Firmware Rootkit: The Malware That Survives a Full OS Reinstall — Why some malware persists below the operating system
- IoT Botnet: Your Smart Cameras Are DDoSing Someone Right Now — How Mirai-style botnets recruit unpatched IoT into DDoS armies
- Living Off the Land: How Attackers Use PowerShell, WMI, and Your Own Tools — Fileless techniques that bypass signature-based detection
- Supply Chain Attack: How SolarWinds Compromised 18,000 Organizations — The trojanized-update vector that bypasses signature controls
→ See all 30 in the Cybersecurity Attacks Series
🎧 Listen to the full episode on Tech Updates or wherever you get your podcasts.