> 🎙️ This post was auto-generated from the [Tech Updates podcast](https://rss.com/podcasts/tech-updates-by-andres-sarmiento/2743984) episode.
In 2022, attackers took 8 hours to move from initial access to launching a secondary attack. By RSAC 2026, that window had collapsed to just 22 seconds. This jaw-dropping statistic—shared by Mandiant on the main stage in San Francisco—encapsulates everything that matters about cybersecurity in 2026: the speed of modern threats has fundamentally changed how we need to defend ourselves.
What This Episode Covers
- Agentic AI as a Security Paradigm Shift — why agents aren’t just smarter chatbots, but autonomous decision-makers that can take action
- The Death of Traditional SIEMs — how agentic systems are replacing legacy security information and event management platforms
- Non-Human Identity & Agent Runtime Control — managing identities for AI agents and controlling their actions in production
- AI-Generated Code Security — new vulnerabilities emerging from AI-assisted development
- Post-Quantum Cryptography — the quiet but critical shift to quantum-resistant algorithms
- Six Critical Predictions — what security leaders need to track over the next 12 months
- The Vendor Landscape — products from Cisco, Microsoft, Palo Alto, Google Cloud, and others positioning themselves in the agentic era
Deep Dive
The 22-Second Problem: Why Speed Changes Everything
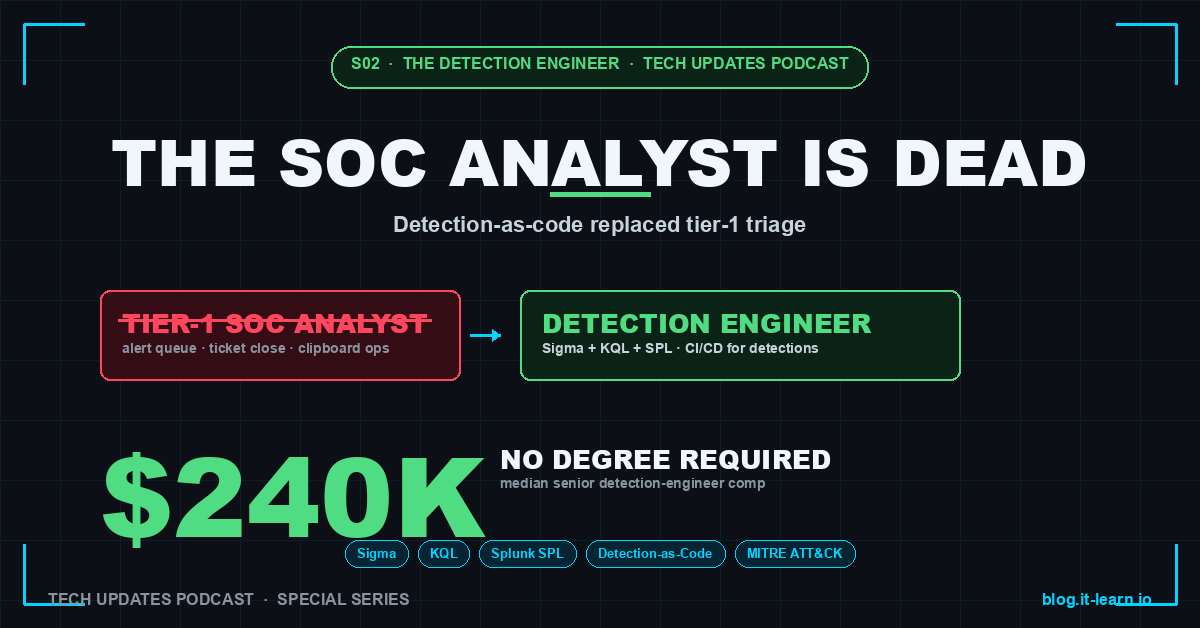
The collapse of the attack-to-exploitation window from hours to seconds is more than a scary statistic—it’s a wake-up call about operational feasibility. Traditional SOCs built around human analysts, ticket queues, and escalation chains cannot respond in 22 seconds. This is why the industry is pivoting so aggressively toward autonomous agents: they can detect, triage, and respond at machine speed.
Agentic AI vs. Chatbots: A Critical Distinction
As Jeetu Patel from Cisco pointed out in the episode: “With chatbots you worry about getting the wrong answer. With agents you worry about taking the wrong action.” This captures the essential difference. A chatbot generates recommendations that a human reviews. An agent executes decisions autonomously—blocking traffic, isolating systems, revoking credentials, running forensics. The stakes are exponentially higher, which is why identity and runtime control have become foundational concerns.
The End of SIEM as We Know It
Ali Ghodsi, CEO of Databricks, made a bold claim on CNBC: “AI will kill the SIEM in 2026.” What does this mean? Traditional SIEMs are log aggregation and search platforms—they collect massive volumes of security events and require analysts to query them. Agentic SIEMs like Databricks’ Lakewatch invert the model: the system continuously hunts, correlates, and acts. Instead of waiting for an analyst to notice something suspicious, the agent proactively investigates anomalies and escalates or remediates based on learned patterns.
This doesn’t mean SIEM vendors disappear, but their positioning shifts from “central repository” to “foundation for agentic platforms.”
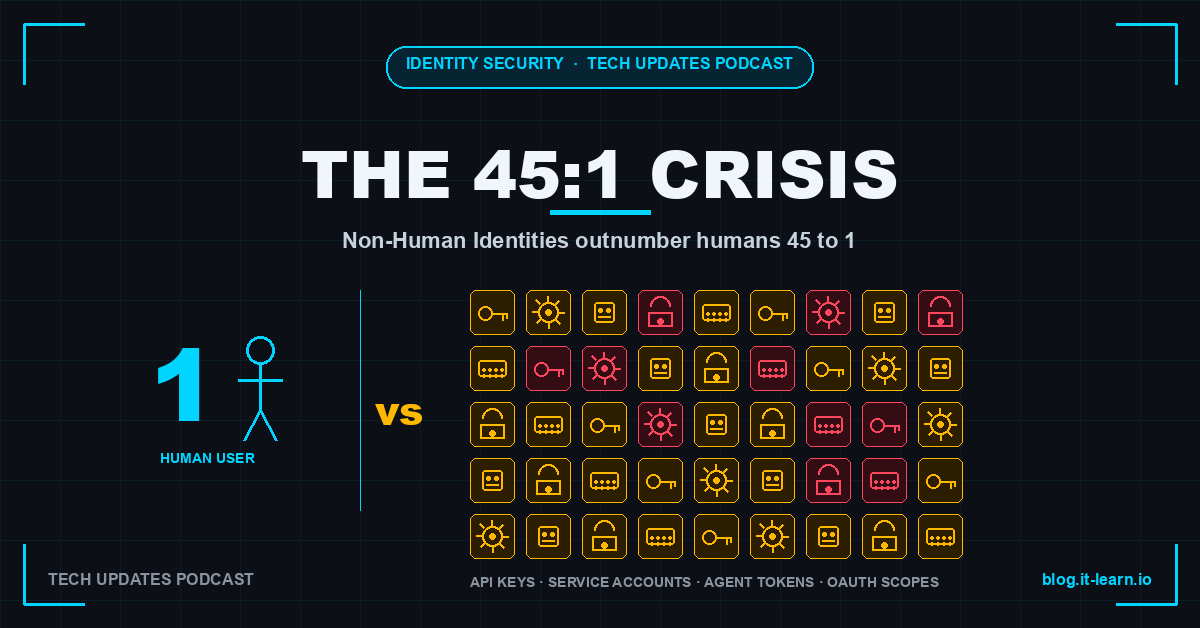
Non-Human Identity: The Next Border War
With agents operating autonomously across your infrastructure, the concept of “identity” becomes infinitely more complex. Microsoft Entra ID, Cisco DefenseClaw, and 1Password are all racing to solve unified access for agents. The problem: who authorizes an agent to access a database? How do you revoke an agent’s permissions without breaking workflows? How do you audit what an agent did?
Prediction #1 on the list—“Non-human identity becomes the primary identity problem”—reflects this shift. Organizations will spend as much effort securing and managing agent identities as they do human ones.
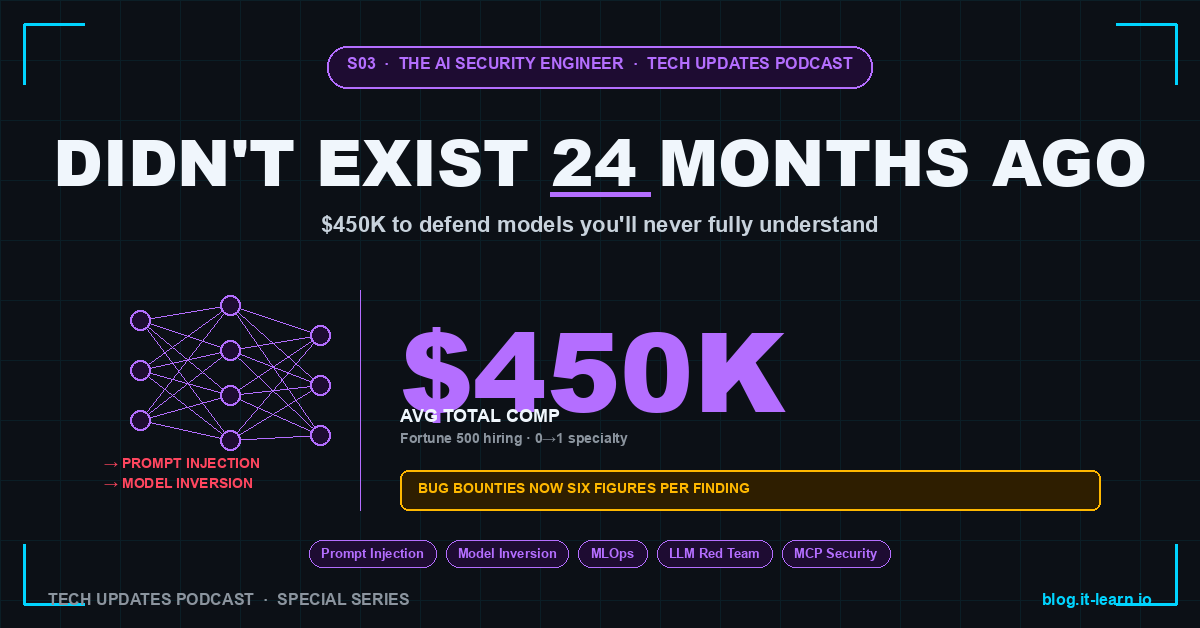
The New Attack Surface: MCP and Prompt Injection
The episode flags two emerging threat categories:
Model Context Protocol (MCP) is being treated like an API gateway. Agents communicate with tools and services through MCP, making it a natural attack surface—similar to how APIs became targets a decade ago.
Prompt Injection (prediction #4) is positioning itself as the next SQL injection. Instead of malicious SQL queries, attackers craft prompts designed to break an agent’s instructions or trick it into taking unintended actions. This is particularly dangerous in security contexts where agents have elevated privileges.
Post-Quantum: Not as Distant as It Seems
Paul Kocher from the 25th Cryptographers’ Panel noted that cryptographic algorithms “have really held up over the last 25 years,” but quantum computing threatens that foundation. Products like ZeroTier Quantum and SandboxAQ AQtive Guard are beginning to offer crypto-agile solutions that can switch between classical and post-quantum algorithms. CNSA 2.0 deadlines are approaching, and this isn’t theoretical anymore.
AI-Generated Code Security & Active Defense
Two additional threads run through the vendor announcements: securing code written by AI tools (Secure Code Warrior, Black Duck Signal) and the resurgence of active defense and deception (Acalvio 360 Deception, Teleport Beams). The former addresses the new vulnerability class introduced by GitHub Copilot and similar tools. The latter represents a philosophical shift: instead of pure prevention and detection, organizations are actively engaging attackers with fake assets.
Key Takeaways
- Agent identity and runtime control are now foundational—your IAM strategy must evolve to account for autonomous systems with elevated privileges
- Speed is the new battleground—if your SOC can’t match 22-second threat timelines, automation is no longer optional
- Prompt injection and MCP are new attack vectors—add them to your threat modeling exercises immediately
- Post-quantum migration is real—begin inventory and evaluation of crypto-agile solutions now, before CNSA 2.0 deadlines force your hand
- The SIEM is evolving, not disappearing—but its role shifts from reactive log storage to foundation for agentic platforms
Why This Matters
The collapse of attack-to-exploitation windows isn’t an abstract threat; it’s a structural challenge to how security operations have been organized for decades. If human analysts cannot scale to match machine-speed attacks, then automation becomes a business continuity imperative, not a nice-to-have. CISOs and engineering leaders who don’t begin piloting agentic SOC capabilities in 2026 risk being operationally outrun within 18 months.
Equally important: the expansion of attack surface—from agents and their identities to prompt injection vectors to MCP gateways—means that traditional perimeter-focused security doesn’t work anymore. The organizations that will thrive are those treating AI agents as
---
🎧 Listen to the full episode on [Tech Updates](https://techupdates.it-learn.io) or wherever you get your podcasts.