Active Directory Persistence: 5 Ways Attackers Stay in Your Domain Forever
Five proven AD persistence techniques — Golden Ticket, Silver Ticket, DCSync, AdminSDHolder, and Skeleton Key — with Mimikatz commands, Event IDs, BloodHound …
Posts tagged: Active-Directory
Five proven AD persistence techniques — Golden Ticket, Silver Ticket, DCSync, AdminSDHolder, and Skeleton Key — with Mimikatz commands, Event IDs, BloodHound …
How attackers forge Kerberos TGTs using the KRBTGT hash for persistent domain access — mechanics, Mimikatz commands, detection, and the double-reset …

Technical deep dive into Pass-the-Hash attacks: NTLM flow, LSASS extraction with Mimikatz, lateral movement with Impacket and CrackMapExec, and defenses …
Complete technical guide to Kerberoasting — Kerberos TGS mechanics, Rubeus and Impacket tooling, hashcat cracking, detection via Event 4769, and gMSA defenses.
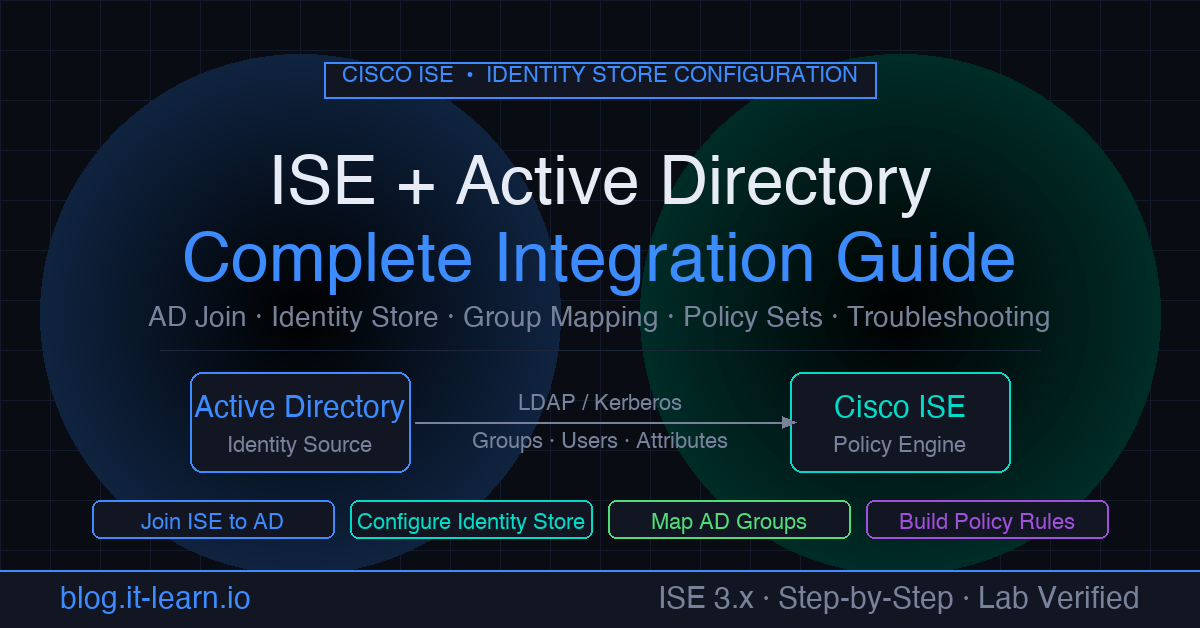
Join Cisco ISE to Active Directory — configure AD as identity store, map AD groups to ISE policies, and troubleshoot common join failures (ISE 3.x).