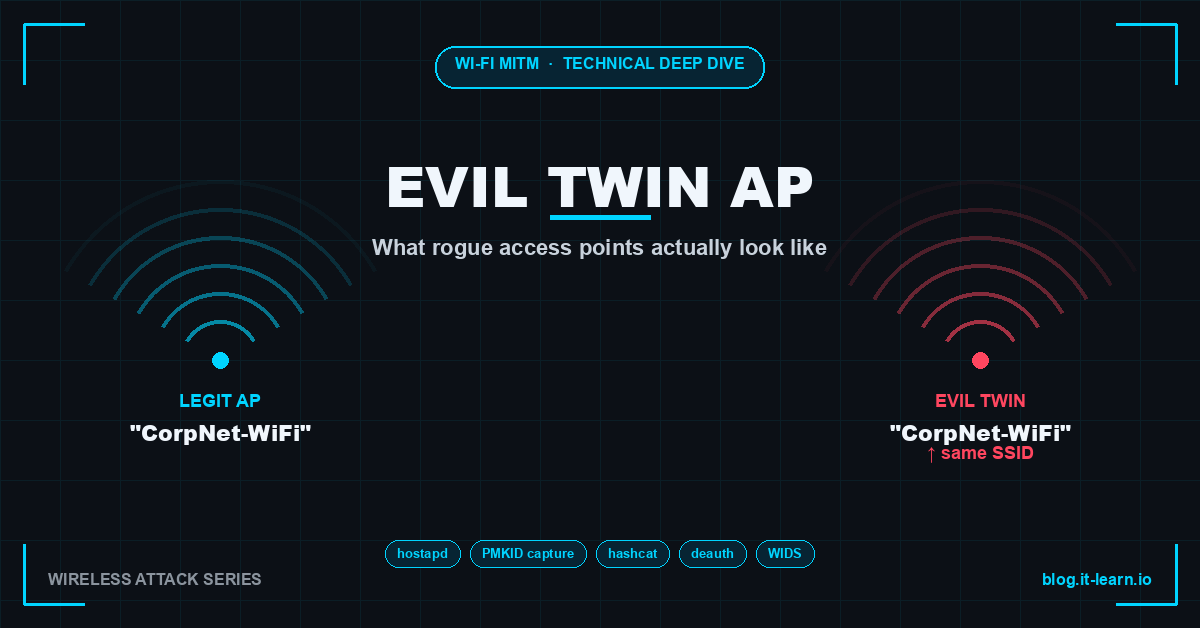
Man-in-the-Middle on Wi-Fi: What Evil Twin Access Points Actually Look Like
Technical deep dive into Evil Twin AP attacks: hostapd setup, PMKID capture, WPA2 cracking with hashcat, deauth floods, and enterprise WIDS defenses.
Posts tagged: Networking
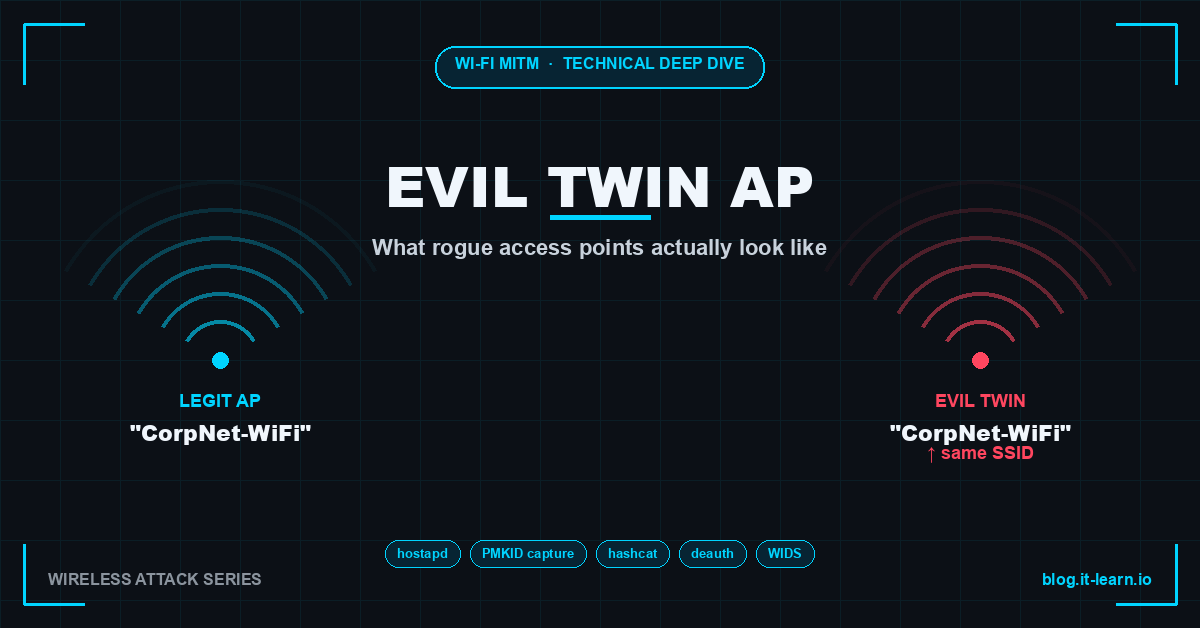
Technical deep dive into Evil Twin AP attacks: hostapd setup, PMKID capture, WPA2 cracking with hashcat, deauth floods, and enterprise WIDS defenses.
Architecture, performance, security, and cost comparison of Cisco SD-WAN vs traditional IPsec VPN — with migration paths, ROI talking points, and customer …
Deep dive into BGP hijacking mechanics, real incidents including the 2018 AWS Route 53 attack, RPKI/ROA validation, BGPStream monitoring, and prefix filtering …

Deep dive into DNS hijacking attack types, real APT campaigns, detection techniques using dig/DNSSEC, and defenses including DNS-over-HTTPS and CAA records.
Configure Cisco ISE guest portals end-to-end — self-registration, sponsored access, hotspot, Central Web Auth flow, and guest VLAN assignment.
Join Cisco ISE to Active Directory — configure AD as identity store, map AD groups to ISE policies, and troubleshoot common join failures (ISE 3.x).
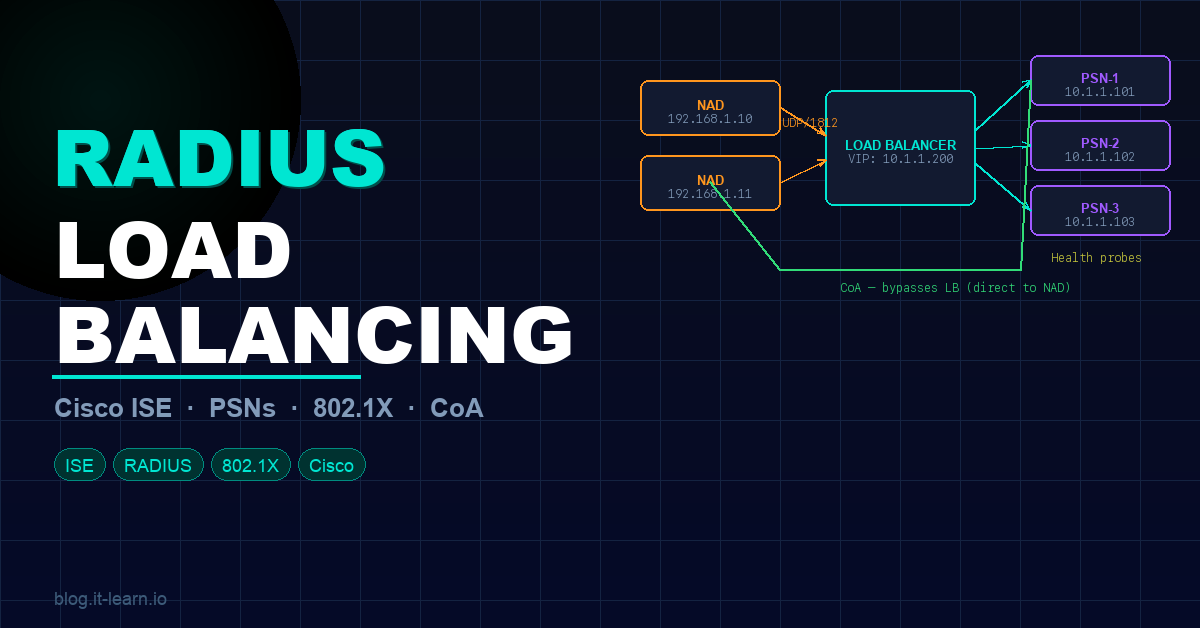
A full breakdown of RADIUS load balancing for Cisco ISE — PSNs, VIPs, session persistence, SNAT pitfalls, health probes, CoA behavior, and cloud LB …
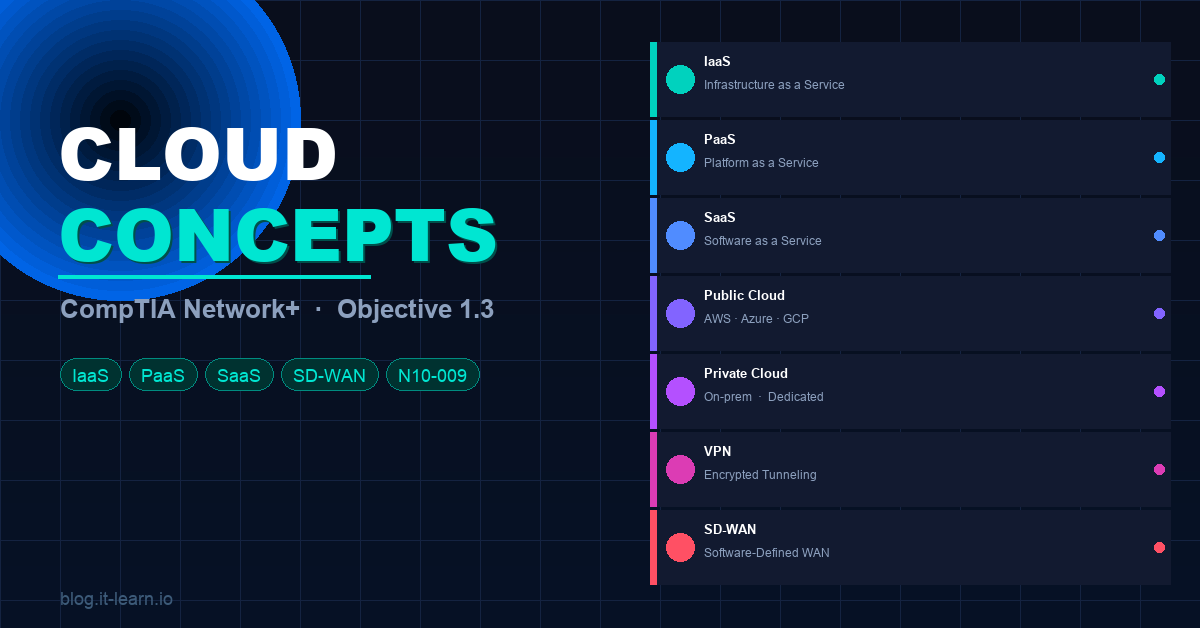
A full breakdown of CompTIA Network+ Objective 1.3 — IaaS, PaaS, SaaS, public/private/hybrid cloud, deployment models, VPN, SD-WAN, MPLS, and connectivity …
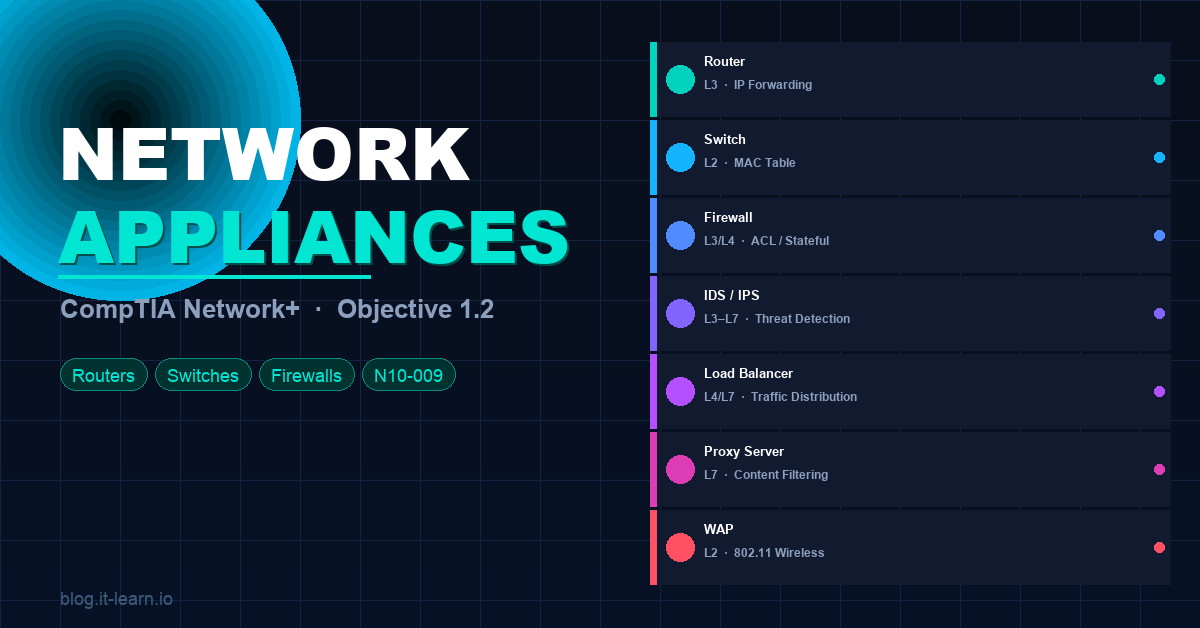
A full breakdown of CompTIA Network+ Objective 1.2 — routers, switches, firewalls, IDS/IPS, load balancers, proxy servers, WAPs, and more. Everything you need …
A hands-on guide to passing the Cisco CCNA 200-301 exam using free and low-cost lab tools — GNS3, Cisco Packet Tracer, and EVE-NG — with real labs for routing, …