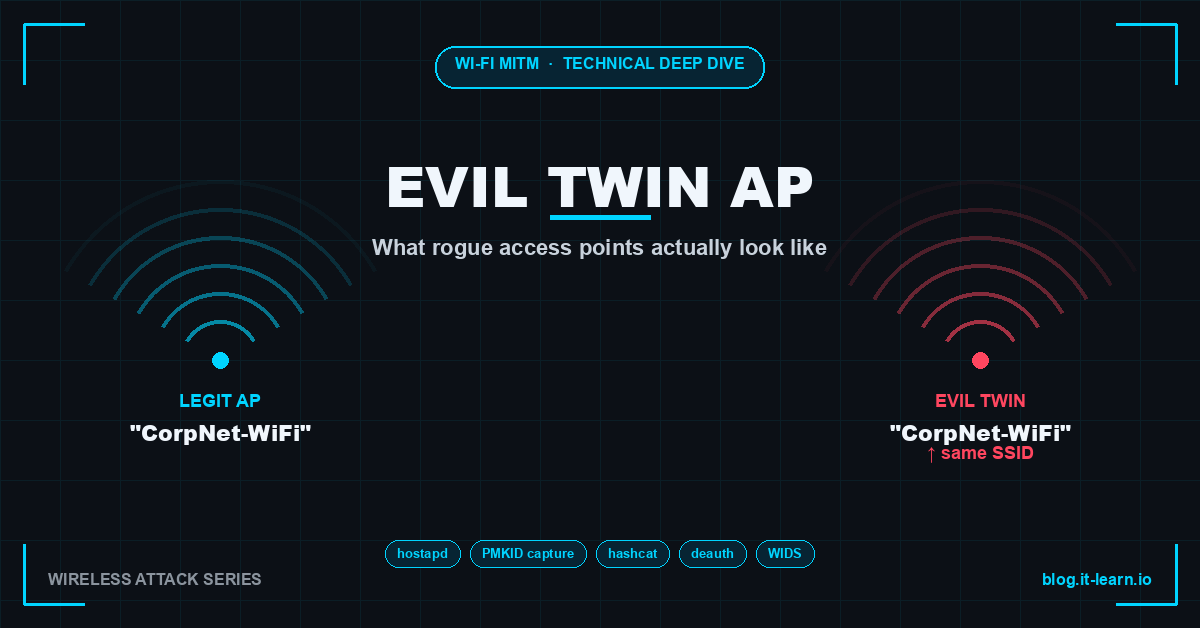
Man-in-the-Middle on Wi-Fi: What Evil Twin Access Points Actually Look Like
Technical deep dive into Evil Twin AP attacks: hostapd setup, PMKID capture, WPA2 cracking with hashcat, deauth floods, and enterprise WIDS defenses.
Posts tagged: Wireless-Security
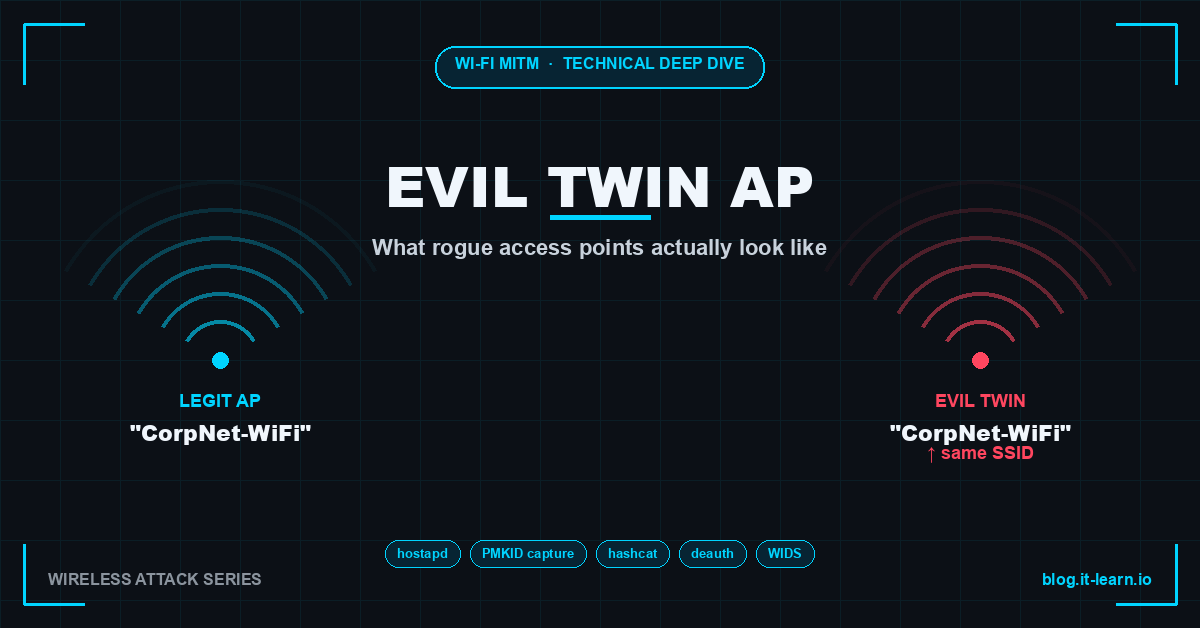
Technical deep dive into Evil Twin AP attacks: hostapd setup, PMKID capture, WPA2 cracking with hashcat, deauth floods, and enterprise WIDS defenses.